IT Asset Disposal (ITAD) is a critical process for businesses in Atlanta, GA, for securely retiring and disposing of obsolete or unwanted technology equipment. It’s an essential operational function that safeguards sensitive corporate data, ensures compliance with federal and state regulations, and manages electronic waste responsibly. A strategic approach to IT asset disposal not only mitigates significant business risks but can also recover financial value from retired corporate hardware.
Understanding the Core of IT Asset Disposal for Atlanta Businesses
For any Atlanta-based enterprise, IT Asset Disposal should be viewed less like simple trash removal and more like the formal decommissioning of a secure data vault. When your company's servers, laptops, desktops, and networking gear are no longer in use, simply storing them in a closet creates a substantial liability. Every one of those retired devices contains a potential data breach, a compliance failure, or an environmental hazard.
A formal ITAD strategy is non-negotiable for modern businesses. It provides a structured, secure, and fully auditable process for managing these end-of-life assets. The objective is to move beyond basic disposal and embrace a comprehensive lifecycle management approach. This ensures that every byte of data is permanently destroyed, every component is recycled in accordance with state and federal laws, and any remaining financial value is captured for your organization.
Why ITAD is a Business Imperative
Ignoring a formal disposal process can have disastrous consequences. Major corporations have faced millions in fines and irreparable brand damage due to data breaches originating from improperly discarded devices. Effective IT asset disposal is a crucial part of a bigger picture known as information life cycle management, which ensures data is handled securely from the moment it’s created to the moment it’s destroyed.
A professional ITAD program addresses several key business needs:
- Data Security: It guarantees the complete and permanent destruction of sensitive company and customer data residing on old hard drives, servers, and mobile devices.
- Regulatory Compliance: It helps your organization adhere to data protection laws like HIPAA, PCI DSS, and the FTC Disposal Rule, providing the necessary documentation to prove compliance.
- Environmental Responsibility: It ensures electronic waste is recycled according to certified standards, keeping hazardous materials out of landfills and supporting your company's sustainability objectives.
- Value Recovery: It identifies functional equipment that can be refurbished and resold, turning retired assets into a revenue stream through buyback programs. You can read more about why proper IT equipment disposal matters in our detailed guide.
To give you a clearer picture, let's break down the essential pillars of a professional ITAD program.
Core Components of a Professional ITAD Strategy
This table summarizes the key pillars of a comprehensive ITAD program, helping you quickly grasp the scope of services involved.
| Component | Business Objective | Example Service |
|---|---|---|
| Secure Logistics | Prevent theft or loss during transit. | GPS-tracked trucks, sealed containers. |
| Data Destruction | Eliminate all sensitive data to prevent breaches. | On-site hard drive shredding, NIST 800-88 data erasure. |
| Asset Reporting | Maintain a clear audit trail for compliance. | Serialized inventory reports, certificates of destruction. |
| Value Recovery | Maximize ROI from retired but functional assets. | Resale of viable equipment, component harvesting. |
| Certified Recycling | Ensure environmental compliance and sustainability. | R2 or e-Stewards certified e-waste processing. |
Ultimately, a strong ITAD strategy integrates all these components to protect your business from every angle.
The Growing Market for Secure Disposal
The explosive growth of the ITAD market shows just how important this has become. The global IT asset disposition market is valued somewhere between USD 17.5 to 18.61 billion and is expected to rocket to over USD 40 billion by 2032. Right now, North America is leading the charge, with large companies driving demand as they decommission massive data centers and wrestle with complex regulations.
This trend highlights a major shift in thinking: businesses now understand that professional ITAD isn’t just a cost, but an essential investment in their security and reputation.
The ITAD Workflow From Pickup to Final Reporting
Ever wonder what really happens to your old IT equipment after it's hauled away? A professional IT asset disposal process is so much more than a simple pickup. It’s a meticulous, fully-documented journey built from the ground up for total security and accountability.
Every single step is tracked, from the moment a device leaves your office to its final recycling or destruction. This isn't just about getting rid of old gear; it's about protecting your data and legally transferring liability away from your organization.
This journey is designed to turn potential risks into secure, compliant, and often valuable outcomes.
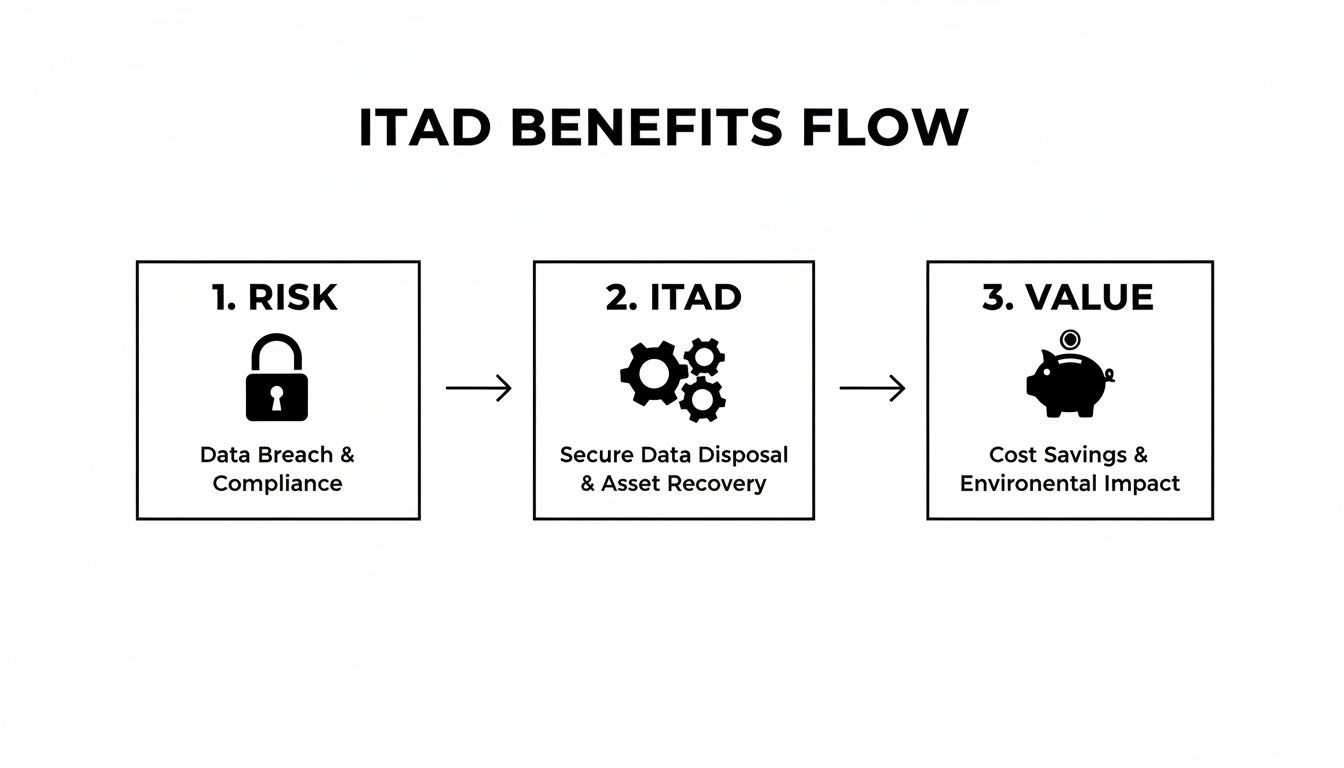
As the flow chart shows, a proper ITAD process is all about systematically turning security headaches into managed operations that can actually create financial value. Let's walk through the key stages to see how it all comes together.
Step 1: Secure Logistics and On-Site Pickup
It all starts with logistics designed around security, not just convenience. A true ITAD partner uses their own fleet of vehicles, often equipped with GPS tracking, to monitor every asset from your front door to their secure facility. This is a security operation, not a standard moving job.
When the team arrives, trained technicians use the right equipment to safely handle everything from a few laptops to entire server racks. Your assets are carefully packed into sealed, tamper-evident containers before they're even loaded, creating the first link in an unbreakable chain of custody. This documented handover is the exact point where the responsibility for that equipment officially transfers from you to your vendor.
Step 2: Meticulous Inventory and Asset Tracking
Once the equipment hits the secure ITAD facility, it's checked in and inventoried with painstaking detail. This isn't just counting boxes; it's a critical step in creating a fully auditable trail. Each device gets a unique identifier, and its serial number is scanned and logged into a sophisticated asset management system.
This detailed inventory serves a few crucial purposes:
- Accountability: It gives you a complete, itemized record of every single piece of hardware received from your business.
- Compliance: That serialized list is your golden ticket for regulatory audits, proving that specific devices were handled correctly.
- Reporting: All this data becomes the foundation for the final reports and certificates you’ll receive later.
Without this step, it would be impossible to prove what happened to a specific hard drive or server. You can see how this structured approach works by reviewing our guide on how the ITAD process works.
"The moment a device is inventoried by serial number, it ceases to be an anonymous piece of hardware and becomes a tracked, accountable asset. This transition from 'old computer' to 'tracked asset' is the bedrock of a secure ITAD program."
Step 3: Guaranteed Data Sanitization or Destruction
Now we get to the most critical stage for shutting down risk. Depending on your security policies and the type of media, there are two main paths for making sure your data is gone for good: sanitization or physical destruction.
Software-Based Data Wiping (Sanitization):
For assets that still have life in them and might be resold, we use specialized software to completely overwrite the hard drive with random data. This process follows strict standards like NIST 800-88, making the original information forensically unrecoverable.
Physical Destruction:
For devices that held top-secret data or are simply too old to function, physical destruction is the only way to go. This isn't just taking a hammer to it; it's a precise process.
- Shredding: Hard drives are fed into industrial shredders that grind them into tiny, unrecognizable metal fragments. There's no coming back from that.
- Degaussing: We use a powerful magnetic field to permanently scramble and erase the magnetic data on traditional hard disk drives (HDDs).
The right choice depends entirely on your company's data security policy and compliance needs.
Step 4: Certified Reporting and Final Documentation
The whole process wraps up with the most important deliverable you'll receive: certified documentation. After every asset has been processed, your ITAD partner issues official certificates that act as legal proof that everything was disposed of by the book.
These essential documents include:
- Certificate of Data Destruction: This report lists the serial numbers of every single hard drive that was sanitized or destroyed, confirming your data was eliminated in line with federal and state regulations.
- Certificate of Recycling: This document verifies that all non-working electronic parts were recycled in an environmentally responsible way, following standards like R2v3.
This final reporting officially closes the loop on your assets' lifecycle. It gives you the auditable proof your organization needs to satisfy auditors, demonstrate due diligence, and legally transfer liability. It’s what lets you sleep at night.
Navigating the Maze of Compliance and Regulations
For any company handling sensitive information, getting rid of old IT gear isn't just an operational task—it’s a legal minefield. One wrong move with a retired server, laptop, or even a copier can trigger massive fines, a public relations nightmare, and painful regulatory audits. The simple act of retiring old equipment is tangled in a complex web of federal and state laws built to protect consumer and patient data.
These rules aren't just suggestions; they’re strict mandates with very real consequences. If you're in healthcare, finance, or government contracting, ignoring compliance is simply not an option. A certified ITAD partner is your shield in this environment, turning dense legal jargon into a documented, auditable process that keeps your organization safe.
The FTC Disposal Rule Explained
At the very least, the Federal Trade Commission (FTC) Disposal Rule touches nearly every business holding consumer information. The rule demands that companies take "reasonable measures" to guard against unauthorized access to that information when it's time for disposal.
So, what’s "reasonable"? It means you can't just toss old hard drives in a dumpster and call it a day. The rule insists that you properly destroy or erase the data on retired devices, making it completely unreadable and impossible to reconstruct. This is exactly where professional ITAD becomes non-negotiable, providing the certified destruction needed to meet this federal baseline.
Industry-Specific Compliance Mandates
Beyond the broad FTC rule, many industries are held to even higher standards. These laws get very specific about the type of data that needs protection and exactly how it must be secured throughout its entire lifecycle—right up to the final disposal.
To give you a clearer picture, here’s how some of the major regulations stack up and what they demand from your ITAD process.
Key Regulations and Their Impact on IT Asset Disposal
| Regulation | Industry Focus | Data Protected | Required ITAD Action |
|---|---|---|---|
| HIPAA | Healthcare | Protected Health Information (PHI) | Data must be rendered "unusable, unreadable, or indecipherable." Simple deletion is not compliant. |
| PCI DSS | Finance, Retail | Cardholder Data | All stored cardholder data must be made unrecoverable when no longer needed for business or legal reasons. |
| FTC Disposal Rule | All Businesses | Consumer Information | Must take "reasonable measures" to destroy data, making it unreadable and non-reconstructable. |
| SOX | Publicly Traded Companies | Financial Records | ITAD processes must be documented and secure to prove financial data was properly destroyed per retention policies. |
As you can see, each regulation has its own focus, but the common thread is clear: data must be irreversibly destroyed, and you need to be able to prove it.
The Importance of NIST 800-88 Standards
To actually meet these tough compliance demands, you need a verifiable standard for data destruction. That's where the National Institute of Standards and Technology (NIST) Special Publication 800-88 comes in. It’s the gold standard for media sanitization, laying out clear, tiered methods for destroying data:
- Clear: This involves overwriting data with new data, usually through software.
- Purge: A more intense method, using advanced overwriting techniques or degaussing (with powerful magnets) to make data recovery infeasible, even with laboratory tools.
- Destroy: The final step. This means physically shredding, disintegrating, or melting the media, which makes data recovery completely impossible.
Working with an ITAD vendor who lives and breathes these guidelines is critical. It guarantees your data destruction process is not only effective but can stand up to scrutiny during an audit. For a more detailed look, you can learn more about NIST SP 800-88 guidelines and see how they apply to your specific equipment.
"In the eyes of regulators, data is not considered 'destroyed' until it is forensically unrecoverable. Relying on employee-led wiping or uncertified vendors leaves a significant liability gap that can easily be exploited."
Ultimately, getting through this regulatory landscape requires a process that is documented, certified, and completely transparent. Things like secure chain-of-custody records, serialized certificates of data destruction, and strict adherence to standards like NIST 800-88 give you the auditable proof you need to protect your business. It turns a compliance headache into a structured, risk-free operation.
Maximizing Value Recovery From Retired IT Assets
It’s a common mistake to see retired IT equipment as just another liability—something you have to pay to get rid of. While security and compliance are absolutely non-negotiable, your old hardware often has a surprising amount of financial value just waiting to be unlocked. When you shift your mindset from a cost center to a potential revenue stream, the entire ITAD process becomes a smart financial move for your business.
This is the whole idea behind IT asset value recovery. It’s where functional devices are carefully tested, graded, and prepped for a second life on the secondary market. Instead of only paying for disposal, you can actually get a return on your original investment, which can directly offset the costs of a secure ITAD program.

The IT Buyback Process Unpacked
The most straightforward way to recover value is through an IT equipment buyback program. This is where an ITAD partner looks at your retired assets and makes you a fair market value offer for anything that’s still functional and in demand. The process is simple, but it takes an expert eye to get you the best possible return.
Here's a quick look at how a typical buyback program works:
- Initial Assessment: It all starts when the ITAD vendor reviews a list of your retired gear to give you a ballpark estimate of its value.
- Secure Logistics: The equipment is then securely picked up and transported to a certified facility for a much more detailed inspection.
- Data Destruction: Before anything else, every single data-bearing device goes through a certified data sanitization process (like a NIST 800-88 compliant wipe) to completely eliminate security risks.
- Testing and Grading: Technicians get hands-on, testing each component to see what works and assessing its cosmetic condition. They assign a grade that helps determine its resale value.
- Final Offer and Payout: You’ll get a detailed report and a final buyback offer based on the audit. Once you accept, your company gets paid.
Taking a closer look at IT equipment buy back services can uncover a surprising amount of cash that would have otherwise been left on the table.
What Determines an Asset’s Value?
Not all old hardware is created equal. A few key things will influence the fair market value of your used IT equipment. Knowing what they are helps set realistic expectations for what you might get back.
The biggest value drivers include:
- Age and Model: It’s no surprise that newer, more recent models of laptops, servers, and networking gear will fetch higher prices.
- Condition: This is huge. A device that is fully working with minimal scuffs is worth a lot more than one with a cracked screen or missing keys. Both function and appearance matter.
- Configuration: The specs inside—like the CPU speed, amount of RAM, and storage size—directly impact the resale price.
- Market Demand: At the end of the day, it comes down to supply and demand. The current need for specific models on the secondary market plays a massive role.
"Every retired asset has a value story. It might be a fully functional laptop ready for a new user, a server with valuable RAM and CPUs, or a broken device containing precious metals. The key is partnering with an expert who knows how to read that story and extract its full value."
Extracting Value from Non-Working Electronics
Even gear that’s broken or too old to be resold can still bring in some money. The value just isn't in the device as a whole—it's in the individual parts.
This is done in a couple of ways:
- Component Harvesting: Technicians can pull out valuable working parts like RAM, CPUs, and power supplies from otherwise dead devices. These components can then be sold individually.
- Precious Metal Recovery: Your electronics are filled with tiny amounts of gold, silver, palladium, and copper. A certified recycler can responsibly extract these materials from circuit boards, turning them into a return based on current commodity prices.
This full-circle approach ensures no potential value gets overlooked, turning your end-of-life IT assets into a positive line item on your balance sheet.
The Role of E-Waste Recycling in Corporate Sustainability
In an age where customers, investors, and employees expect accountability, how you handle old IT equipment speaks volumes about your company's values. IT asset disposal is no longer a footnote in an operations manual; it's a core pillar of modern corporate social responsibility (CSR) and a huge piece of the puzzle for hitting your environmental, social, and governance (ESG) goals.
This is about more than just checking a compliance box. A smart, forward-thinking ITAD program actively shows your commitment to a sustainable future. It turns what could be an environmental liability into a powerful asset for your brand.

From Landfill Liability to Circular Economy Leader
Let's be blunt: the environmental damage from improperly discarded e-waste is severe. When old computers, servers, and phones are dumped in landfills, they leach toxic heavy metals like lead and mercury straight into the soil and groundwater. That causes long-term ecological harm. This old-school "take-make-dispose" model just isn't sustainable, and regulators and the public are paying close attention.
Professional ITAD gives you a direct path to a more sustainable, circular economy. Instead of becoming hazardous waste, retired assets are given a new purpose.
- Resource Conservation: Certified recycling pulls valuable materials like gold, silver, copper, and aluminum from old circuit boards and components. This means we don't have to rely as much on destructive mining operations to get new raw materials.
- Energy Reduction: Think about it—refurbishing and reusing a functional piece of equipment takes far less energy than manufacturing a brand-new device from scratch.
- Carbon Footprint Reduction: A documented, responsible recycling program gives you real data to put in your sustainability reports. You can show a measurable reduction in your company's environmental impact.
The e-waste problem is exploding, and it's driving huge demand for ITAD. The global e-waste management market jumped from USD 70 billion to USD 81.27 billion in just one year. Experts predict we'll see 50 million tons of e-waste generated annually, yet only 20% of it is recycled properly. That's a lot of toxic materials like lead at risk of contaminating our environment.
Proper ITAD isn't just about waste; it's about value. It recovers billions in assets each year, can cut carbon footprints by 80% through reuse, and strengthens data security. For any IT manager trying to balance costs, compliance, and green initiatives, that's a winning combination.
Meeting ESG Goals Through Responsible ITAD
Investors and stakeholders are increasingly using ESG metrics to judge a company's long-term health and ethical backbone. Your ITAD program is a direct contributor to the "E" in ESG.
Partnering with a certified e-waste recycler like Beyond Surplus provides the auditable documentation—like Certificates of Recycling—you need to back up your ESG claims. This is concrete proof of your commitment to preventing pollution and managing resources sustainably.
Beyond just the mechanics of recycling, it helps to understand the bigger picture. This ultimate guide to ESG strategies for sustainability can offer some great context.
When you weave your ITAD practices into a larger ESG framework, you send a clear signal. It says your organization is proactive, responsible, and in tune with modern business ethics. This isn't just about "doing the right thing"—it's about building a resilient brand that's invested in a healthier planet.
How to Choose the Right IT Asset Disposal Partner
Picking an IT asset disposal vendor is a serious business decision, one that directly affects your company's security, compliance, and even its public reputation. This isn't like hiring a moving company; you're handing over devices packed with your most sensitive corporate and customer data. One wrong move here can spiral into catastrophic financial and legal trouble.
The right partner becomes an extension of your security and compliance teams. They bring the expertise, certified processes, and auditable paper trail you need to legally transfer liability away from your organization, ensuring every single asset is handled responsibly from beginning to end.
Verify Industry-Leading Certifications
Certifications are completely non-negotiable. They are the single most reliable way to know a vendor follows strict, third-party audited standards for data security, environmental responsibility, and worker safety. Without them, you're just operating on promises instead of solid proof.
Before you even think about engaging a potential partner, demand to see evidence of these key certifications:
- R2v3 (Responsible Recycling): This is the gold standard for electronics recycling. It guarantees that e-waste is managed in an environmentally sound and secure way, covering everything from data sanitization to banning the export of hazardous materials.
- e-Stewards: Another top-tier certification, e-Stewards is famous for its tough standards on preventing illegal e-waste exports and ensuring responsible recycling practices.
- NAID AAA: This certification is laser-focused on one thing: secure data destruction. A NAID AAA certified vendor goes through unannounced audits to verify their processes for shredding, wiping, and degaussing meet the absolute highest industry benchmarks.
Think of these certifications as the baseline for trust. They show a vendor is truly committed to professional excellence.
Scrutinize Data Destruction Standards and Physical Security
Your number one goal with IT asset disposal is the complete and permanent destruction of sensitive data. It’s absolutely critical to understand exactly how a potential vendor makes this happen. Don't let them get away with vague assurances; ask for specific details on their methods.
"A vendor's data destruction process should be as transparent and auditable as your own internal security protocols. If they can't provide detailed, serialized proof of destruction, they can't guarantee your compliance."
Insist on a partner who sticks to NIST 800-88 guidelines, the federal government's benchmark for media sanitization. This means they should offer multiple destruction methods—software wiping, degaussing, and physical shredding—to match the sensitivity of your data. For a deeper look at vetting potential partners, our guide on choosing from the top IT asset disposition companies offers more valuable tips.
On top of that, check out their physical security. Ask about the facility's surveillance systems, who has access, and what their employee background check process looks like. A secure chain of custody starts the moment your assets leave your building and relies entirely on the vendor's ability to keep them safe until they're processed.
Evaluate Logistics Capabilities and Reporting
A vendor’s logistics network and reporting skills are just as important as their certifications. An experienced partner should have their own fleet of secure, GPS-tracked vehicles and use their own trained technicians—not third-party movers. This is the only way to ensure a secure and unbroken chain of custody from your facility to theirs.
Finally, detailed and transparent reporting is the ultimate proof that the job was done right. A reputable ITAD partner must provide:
- A serialized inventory of every single asset they collected.
- A Certificate of Data Destruction that lists each hard drive that was sanitized or shredded.
- A Certificate of Recycling that confirms responsible environmental processing.
This stack of documents is your proof of due diligence. It protects your business during an audit and verifies you’ve complied with regulations like HIPAA, PCI DSS, and the FTC Disposal Rule. Choosing a partner who delivers this level of detail is essential for true peace of mind.
IT Asset Disposal FAQs for Atlanta Businesses
Let's wrap things up by tackling some of the most common questions that pop up when businesses start thinking about IT asset disposal. Getting these details right is the key to a smooth, secure process.
What Are the Biggest Risks of Improper IT Asset Disposal?
Ignoring a proper ITAD process opens your business up to some serious headaches. The biggest one by far is a data breach. Think about it—sensitive company secrets or customer information lifted from a supposedly "dead" hard drive. That single mistake can lead to crippling fines for not complying with regulations like HIPAA or the FTC Disposal Rule.
But the danger isn't just digital. E-waste is packed with hazardous materials. Dumping it improperly can land you in legal hot water for environmental violations and do a number on your company's reputation. A certified ITAD process is your shield against all these threats at once.
Is Wiping a Hard Drive Enough to Secure Data?
For many situations, yes, but it’s not a one-size-fits-all answer. A professional, software-based wipe that meets NIST 800-88 standards is usually solid for most business equipment, especially if those assets are going to be refurbished and resold.
However, when you're dealing with extremely sensitive data or certain types of hardware like solid-state drives (SSDs) that can hang onto data fragments, physical destruction is the only way to be 100% certain. The best approach is always to match the destruction method to your company's unique security policies and compliance needs.
What Regulations Require Secure IT Asset Disposal?
Several major federal and industry-specific rules demand secure ITAD. It's not just a good idea; it's the law. Here are a few of the heavy hitters:
- HIPAA: For healthcare, patient data must be made completely unusable and unreadable.
- PCI DSS: If you handle credit cards, cardholder data has to be securely destroyed when you no longer need it.
- FTC Disposal Rule: This one applies to nearly every business and requires "reasonable measures" to destroy consumer information.
- SOX: Public companies have a duty to protect financial records throughout their entire lifecycle, right up to disposal.
Getting this wrong can lead to huge financial penalties and serious legal trouble.
A professional ITAD vendor doesn't just recycle hardware; they provide a documented, legally defensible process that proves your organization met its compliance obligations.
How Do I Verify My Data Has Been Properly Destroyed?
Proof is everything. A secure IT asset disposal strategy is built on verification, and your ITAD partner absolutely must give you official documents that create an audit trail.
You should always demand a Certificate of Data Destruction. This document is your proof of due diligence, listing the unique serial numbers of every single device that was sanitized or destroyed. Without this certificate, you have no way to legally prove your data was handled correctly if an auditor comes knocking.
Contact Beyond Surplus for certified electronics recycling and secure IT asset disposal in Atlanta, GA. Contact us today to schedule a pickup and protect your organization's most valuable assets.