Old laptops in a locked closet. Decommissioned servers on a pallet. A few network switches nobody wants to touch because no one is fully sure what data is still on them. That’s the point where many IT directors open a browser and type e-recycling near me.
For a business, that search usually creates more risk than clarity. Most results are built for household drop-offs, not chain-of-custody, audit support, or asset value recovery. If you’re responsible for security, compliance, and budget, disposal isn’t a cleanup task. It’s part of your IT control environment.
Why a Business Needs More Than a Simple Search
A generic local recycler may be fine for a broken keyboard. It’s not enough for company laptops, storage arrays, retired medical workstations, or gear pulled from a server room. The difference is simple. Your business doesn’t just need removal. You need documented transfer of custody, verified data destruction, and proof that assets were processed correctly.

In 2022, the world generated 62 million tonnes of e-waste, but only 22.3% was formally collected and recycled, according to the Global E-waste Monitor summary cited here. For businesses, that means a large volume of electronics still moves through channels with weak controls, poor documentation, or no meaningful data-security process at all.
What usually goes wrong
The first mistake is treating old IT assets like junk removal. They aren’t junk until you’ve classified them, sanitized them, and documented disposition.
The second mistake is storing them indefinitely. If your team is already looking for business storage near me because retired equipment is stacking up faster than you can process it, that’s often a signal your disposal workflow is broken, not that you only need more room.
Practical rule: If an asset once held company data, the recycler’s process matters as much as the pickup.
A proper vendor review should cover data destruction standards, transport controls, certificates, and downstream processing. If you need a framework for that review, use a documented ITAD vendor due diligence checklist before you schedule anything.
The business issue isn’t recycling alone
Consumer-focused advice talks about keeping electronics out of landfills. That matters, but it’s not your main operational problem.
Your core questions are different:
- Will data be destroyed properly
- Will the provider give you audit-ready documentation
- Can they handle volume from office refreshes or data center work
- Can remarketable assets be recovered for value instead of scrapped
Those are ITAD questions, not household recycling questions. If your search for e-recycling near me doesn’t answer them, keep looking.
Finding Potential Commercial E-Recycling Partners in Atlanta
Start by changing the search itself. “E-recycling near me” is too broad for an Atlanta business with racks, endpoint fleets, or regulated data. Use commercial intent terms that force better results.

Search like a buyer, not a resident
Try combinations such as:
- Atlanta IT asset disposition
- Atlanta certified data destruction
- enterprise electronics recycling Atlanta
- data center decommissioning Atlanta
- medical equipment disposal Atlanta
- IT equipment pickup Atlanta
Those phrases filter out pages built around weekend drop-offs and municipal events. They also surface providers that speak the language of asset tracking, de-installation, and reporting. A commercial-focused search can also be a shortcut to resources on IT recycling near me for businesses, which is closer to what most IT directors need.
Read the service page like an auditor
Don’t stop at the headline. Scan the page for signs the provider works with organizations, not just individuals.
Look for these markers:
- On-site options for drive shredding or pickup from offices, clinics, warehouses, and data centers
- Industry language tied to healthcare, finance, education, government, or enterprise environments
- Documentation references such as chain-of-custody records, certificates of destruction, certificates of recycling, serialized reporting
- Logistics capability including palletized pickups, de-install support, and multi-site coordination
If a page talks mostly about “free drop-off,” “household items,” or event-based recycling, it’s probably not designed for your environment.
A commercial recycler should make risk controls visible before you ever call them.
Build a shortlist fast
Use a simple three-column screen:
| Provider signal | Keep on shortlist | Remove from shortlist |
|---|---|---|
| Business focus | Mentions offices, enterprises, regulated industries | Talks mainly about residents and household drop-offs |
| Security process | Explains wiping, shredding, or reporting | Says “secure” without saying how |
| Operational fit | Offers pickup, de-install, or fleet support | Requires you to do all transport and sorting |
A good Atlanta shortlist is usually small. That’s fine. You don’t need a long list. You need vendors that can survive scrutiny.
Vetting Providers for Security and Compliance
A vendor can sound polished on a call and still expose your company to preventable risk. The test is whether they can show you how custody, data destruction, downstream recycling, and liability transfer work in practice.
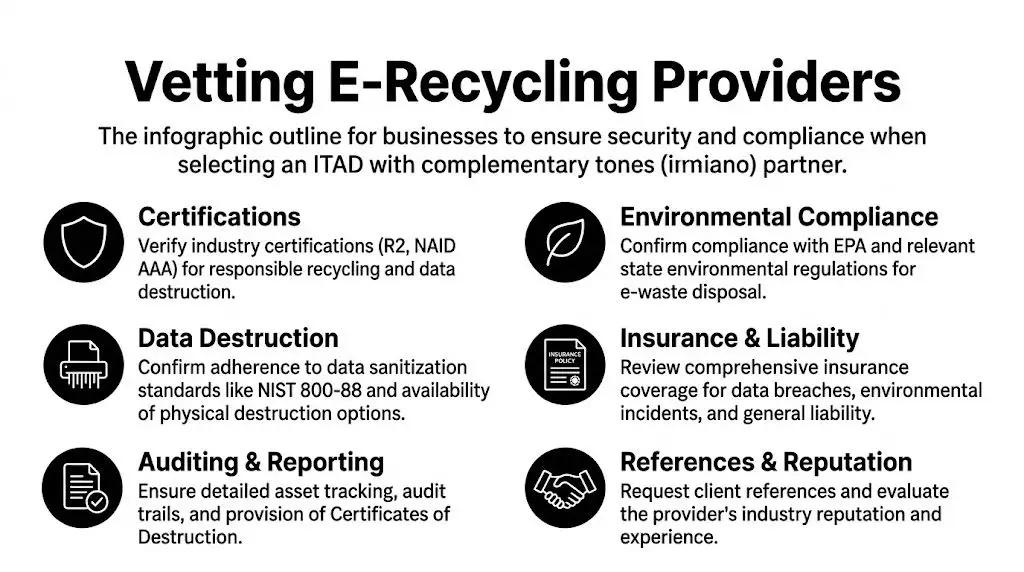
Ask what their certificates actually do
Certificates matter only if they tie back to a documented event. You need records that show what was picked up, how items were tracked, which assets were destroyed or sanitized, and when custody changed hands.
Many business teams accept a certificate of destruction as a generic receipt. That is a mistake. If your legal, compliance, or security team ever has to defend the disposition process, the document needs enough detail to support that review. The FTC Disposal Rule issue is not whether a recycler uses the word "secure." It is whether the provider can prove what happened to each data-bearing asset through chain-of-custody and final reporting, as discussed in this review of electronics recycling compliance documentation.
Certifications matter only if operations match the claim
A logo on a website is a starting point, not evidence. If a provider references R2, e-Stewards, or NAID AAA, ask how those standards appear in intake, processing, storage, destruction, reporting, and downstream vendor management.
A useful answer includes specifics such as:
- NIST 800-88 data sanitization for equipment slated for reuse
- Physical shredding for drives and media that your policy requires destroyed
- Serialized asset tracking from pickup through final disposition
- Exception handling for damaged devices, locked systems, and unidentified media
- Documented environmental controls for downstream recycling
If your stakeholders need context, this explainer on R2 certification and what it covers helps clarify why process controls apply to both data security and responsible recycling.
Trace the handoff before you sign anything
Ask the provider to walk through a single laptop, server, or loose hard drive from your dock to final report. Good operators can explain that flow without hesitation. Weak vendors answer in generalities.
The sequence should be clear. Pickup, packaging control, transport, intake, scan, data destruction or sanitization, testing if applicable, remarketing or material recovery, and final documentation. That operating discipline is what separates business ITAD from consumer drop-off recycling, as outlined in this breakdown of IT asset recycling methodology.
Transportation risk also deserves attention. If the provider is moving pallets of data-bearing equipment across state lines, ask what coverage applies in transit and review whether they carry motor truck cargo insurance or rely on a carrier arrangement that leaves gaps. Data loss, theft, and physical damage claims get complicated fast once equipment leaves your site.
Questions that expose weak vendors
Use questions that force the provider to describe actual controls.
- What happens to a laptop from pickup to final disposition
- How do you identify and segregate data-bearing devices at intake
- When do you wipe, and when do you shred
- What fields appear on your chain-of-custody record
- Can you support on-site destruction if our policy requires it
- What final documents will we receive, and how quickly
Listen for precision. If the answer stays at the slogan level, remove that vendor from consideration.
One commercial option in Atlanta
For comparison, Atlanta-based ITAD providers like Beyond Surplus offer services including on-site shredding, certified data wiping, and IT buyback with nationwide business pickup.
That kind of service mix is relevant because business recycling decisions are rarely about recycling alone. You are choosing a vendor that may handle regulated data, transport insured equipment, and determine whether retired assets become audit evidence, resale recovery, or scrap.
What strong vetting looks like
The right provider explains controls in operational terms and backs them with records. The wrong provider leans on broad words like "green," "secure," or "certified" without showing how those claims hold up during pickup, processing, and reporting.
Security and compliance require evidence. For businesses, that is the standard that matters.
Preparing Assets to Maximize Value and Security
Too many companies assume every retired device belongs in the scrap stream. That’s expensive thinking. Some assets should be destroyed immediately. Others should be wiped, tested, and remarketed. If you don’t separate those paths early, you lose both control and value.
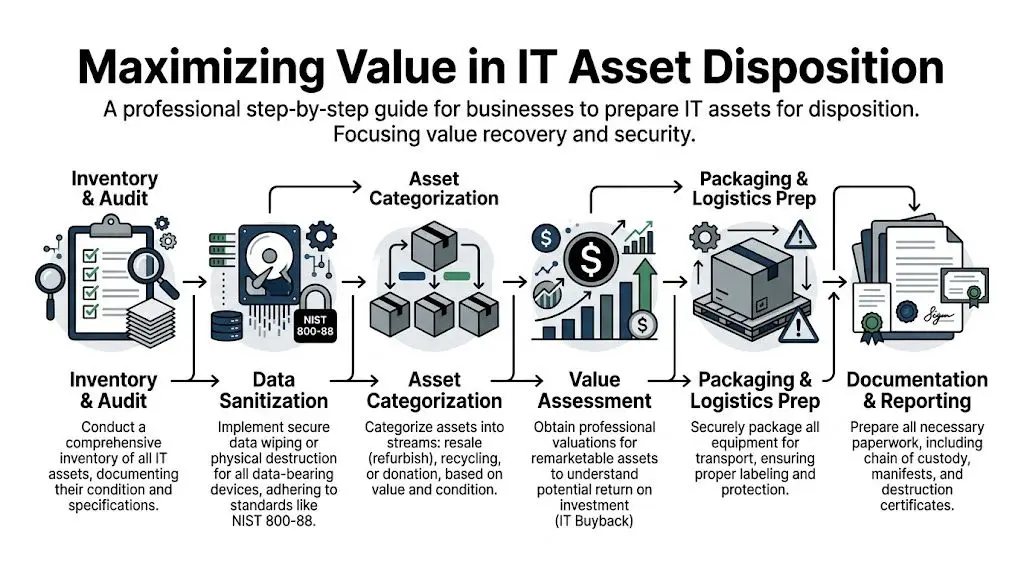
Globally, 40% of electronics in the e-waste stream are still functional. Businesses often miss the chance to recover 20-50% of original asset costs because generic local recycling services don’t offer certified buyback programs, according to this discussion of electronics reuse and IT buyback value.
Separate devices before pickup
Don’t hand your vendor a mixed pile and hope for the best. Build an internal inventory first.
A practical pre-pickup sort looks like this:
- Remarketable equipment such as newer laptops, desktops, servers, and network gear that may still hold resale value
- Data-bearing devices for destruction including failed drives, SSDs, backup media, and anything your policy says must be shredded
- Low-value scrap such as obsolete peripherals, damaged units, cables, and non-redeployable hardware
This internal sort helps your finance team, your security team, and the vendor. Everyone sees the same asset picture before the truck arrives.
Add controls before the handoff
If your team can perform approved internal prep, do it. Remove retired assets from active directories and inventory systems. Flag leased equipment. Mark anything with legal hold implications. Keep device counts aligned with pickup paperwork.
For transport risk, it also helps to understand how motor truck cargo insurance works, especially if your assets move between sites or through third-party carriers. The point isn’t to become an insurance expert. It’s to know what questions to ask when equipment leaves your custody.
Wiping a hard drive is only half the control. The other half is proving which drive was wiped, when, and under whose custody.
If your team needs a refresher before staging devices, use a practical guide on how to completely wipe a hard drive and align it with your provider’s documented process.
Value recovery starts with discipline
Buyback isn’t accidental. It depends on clean records, complete units, and fast disposition before equipment ages out further. The companies that recover value don’t just “recycle better.” They identify the resale stream early and protect it.
Coordinating Logistics for Secure Nationwide Pickup
Pickup day should be boring. If it feels chaotic, the planning was weak.
For business e-recycling near me, logistics are where weak vendors get exposed. They may accept a list of assets but struggle with loading dock coordination, pallet counts, serialized scans, or multi-site timing. That’s where costs rise and documentation breaks.

Logistical challenges such as device complexity and soldered batteries can inflate costs by 25% if they aren’t handled by a professional ITAD service. Certified firms also achieve 97% material diversion rates versus 52-56% at municipal facilities, according to this analysis of e-waste collection challenges and professional processing.
What to lock down before the truck arrives
Use a short operational checklist:
- Pickup scope confirmed with site address, contact, dock access, stairs, elevator limits, and asset volume
- Packaging plan decided for pallets, gaylords, carts, or room-by-room de-install removal
- Scan protocol defined so you know whether assets are counted by pallet, by item, or by serialized device
- Security controls assigned including escort requirements, badge access, and restricted areas
A provider that offers nationwide reverse logistics services for IT assets is usually better equipped for multi-site pickups, consolidations, and standardized reporting.
What good handoff documentation looks like
You should expect a clear pickup record, not a vague “we got it” message. Depending on the project, that may include asset manifests, serialized logs, pallet counts, service acknowledgments, and final destruction or recycling certificates.
The handoff isn’t complete when the truck leaves. It’s complete when your records team can match the pickup to the final disposition documents.
For Atlanta companies with branch locations elsewhere, this matters even more. The best logistics model is one process across all sites, not a different recycler in every market.
Frequently Asked Questions for Business E-Recycling
| Question | Answer |
|---|---|
| Do I need an ITAD provider or just a recycler? | If the equipment held company data or has resale value, you need ITAD-level controls. Recycling is one outcome. The bigger requirement is documented disposition. |
| Can leased equipment go into the same pickup as owned assets? | Yes, if you separate and label it clearly. Your finance and procurement teams should confirm return obligations before pickup. |
| Should we wipe drives ourselves before pickup? | You can, if your policy and tooling support it. Many organizations still require the downstream provider to perform documented wiping or shredding so the final record sits with the disposition event. |
| What if we’re decommissioning a server room, not just clearing a storage closet? | Use a provider that can handle de-installation, serialized tracking, and staged logistics. Data center work needs more planning than routine office pickups. |
| Is local pickup enough if we have multiple offices? | Usually not. Multi-site companies benefit from one standardized process, one reporting format, and one escalation path. |
| What documents should I require at the end? | Ask for chain-of-custody records, destruction documentation for data-bearing assets, and recycling documentation for processed equipment. Your exact package should match your internal compliance requirements. |
| Can old equipment still have value even if we planned to scrap it? | Often yes. The decision should be based on condition, age, configuration, and marketability, not on whether the asset is merely retired from your environment. |
If you’re evaluating e-recycling near me for your business, start with controls, not convenience. Beyond Surplus supports organizations that need secure IT asset disposition, data destruction, electronics recycling, and value recovery with documented chain-of-custody and business pickup options.