At its most basic, a degausser is a powerful machine that blasts magnetic storage media like hard drives and tapes with an intense magnetic field, wiping them clean permanently. This isn't just deleting a file; it's a complete, irreversible sanitization. For any business that handles sensitive data, understanding what a degausser is provides a serious edge in security.
The Foundation of Magnetic Data Erasure

Picture your hard drive's platter as a massive canvas covered in tiny magnetic particles. To store your data, each of these particles is carefully arranged with a specific north-south polarity, representing the ones and zeros that make up your files. A degausser is like a giant magnetic reset button. It hits that canvas with such an overwhelming magnetic force that it scrambles every single particle into a totally random, unreadable mess.
This is worlds apart from just deleting a file on your computer. When you hit "delete," your operating system is really just removing the signpost that points to where your data lives. The actual magnetic patterns—the data itself—are still there, just waiting to be recovered. Degaussing, on the other hand, utterly destroys the magnetic structure of that data, making recovery impossible, even for forensic experts with high-tech tools.
Why This Matters for Your Business
This distinction is absolutely critical for any organization handling proprietary information, customer records, or regulated data. Simply deleting files or formatting drives before getting rid of old IT equipment leaves gaping security holes. All it takes is one discarded hard drive with recoverable data to trigger a devastating breach, leading to massive fines and a shattered reputation.
Degaussing should be a cornerstone of any secure data sanitization program and a key part of a responsible IT Asset Disposition (ITAD) strategy. It brings a few major benefits to the table for any enterprise:
- Absolute Data Destruction: It delivers verifiable proof that the data on your magnetic media is gone forever.
- Compliance Assurance: This method is a proven way to meet strict data privacy regulations like HIPAA, GDPR, and the FTC Disposal Rule.
- Speed and Efficiency: A good degausser can sanitize a hard drive in just a few seconds, making it a perfect tool for processing large batches of retired assets.
By neutralizing the magnetic field on the media, degaussing permanently erases all data and formatting by randomizing the magnetic domains. This provides an absolute certainty that your retired data is gone for good, transferring liability away from your organization.
Ultimately, building degaussing into your protocols for end-of-life equipment is a proactive defense against data breaches. It adds a crucial layer of security that software-based wiping can't always promise, especially when you're dealing with drives that are damaged or have failed. For businesses that need a certified, auditable way to protect their most valuable digital assets, understanding and using degaussing technology isn't optional. It's a fundamental tool for managing risk in a data-driven world.
From Naval Warfare to Data Centers The Surprising History of Degaussing
The degausser protecting your company’s data today has a fascinating and unexpected origin story. It wasn’t born in a quiet server room but forged in the heat of conflict on the high seas during World War II. Its original mission? To make massive steel warships invisible to a deadly new threat: magnetic sea mines.

This journey from naval warfare to data security is a powerful real-world testament to the sheer force of magnetic field manipulation and why it’s still so relevant today.
The Dawn of Magnetic Warfare
The core principle behind degaussing emerged as a critical naval countermeasure. While the British had tinkered with magnetic mines back in 1919, it was the Germans who perfected the technology, creating mines with highly sensitive triggers that detected the natural magnetic field of a ship passing overhead. When World War II kicked off, these weapons became an unprecedented threat to Allied naval and merchant fleets.
The game changed in November 1939, when a German magnetic mine washed ashore on the Thames estuary. British scientists carefully dismantled the device, uncovering its advanced trigger mechanism. This breakthrough led to an ingenious solution: wrapping the hulls of ships with massive electrical cables. By running a current through these cables, they could create a new magnetic field that canceled out the ship's own, effectively cloaking it from the mine's sensors. By 1940, this technology was rolled out across thousands of vessels, saving countless lives and ships. You can learn more about the history of magnets and degaussing ships from this period.
Transitioning From Ships to Storage Media
The same fundamental physics used to protect a 40,000-ton battleship is now applied at a microscopic level to protect your data. This transition from the battlefield to the data center proves just how reliable the technology is. Just as degaussing scrambled a ship's magnetic signature to fool a mine, a modern degausser scrambles the microscopic magnetic particles on a hard drive platter to permanently destroy data.
The evolution was all about adapting the scale and precision of the magnetic field.
- Naval Application: The goal was to broadcast a large, external magnetic field to neutralize the ship's signature from a distance.
- Data Destruction Application: The goal is to generate an intensely focused magnetic field to overwhelm and randomize the tightly packed magnetic domains on a drive's surface.
This leap shows how a wartime necessity became an indispensable tool for corporate data security. The magnetic forces that once protected national security now protect your company’s most sensitive digital assets.
The core concept remains unchanged: a powerful, controlled magnetic field can be used to alter existing magnetic properties. Whether applied to a massive steel hull or a tiny hard drive platter, the result is a state of magnetic neutrality.
This shared history underscores the robust and reliable nature of degaussing. The technology has been tested and refined for over 80 years, proving its effectiveness under the most demanding conditions. When you choose degaussing for your IT asset disposition strategy, you aren't just using a modern tool; you're leveraging a battle-proven principle of physics to ensure your information is gone for good.
How Degaussing Achieves Permanent Data Erasure
To truly grasp why degaussing is the final word in data destruction, you have to understand how magnetic storage works. The data on your old hard drives (HDDs) and backup tapes isn't just an abstract digital concept—it's physical. Millions of tiny magnetic particles are painstakingly arranged into specific patterns to represent all those ones and zeros.
A degausser works on a simple, brute-force principle. It generates an incredibly powerful magnetic field, one that's exponentially stronger than the field originally used to write the data. When a drive or tape gets hit with this force, those carefully arranged data patterns are violently scrambled beyond recognition.
Exceeding Coercivity: The Point of No Return
Scientifically, this process is called exceeding the media’s coercivity. Coercivity is simply how resistant a magnetic material is to being demagnetized. Think of it as the "magnetic grip" holding your data in place. To truly erase that data, you must hit it with a magnetic field strong enough to break that grip completely.
A degausser doesn't just delete files or write new data over the old. It attacks the physical foundation of the data itself, scrambling the magnetic particles so thoroughly that the original information is gone forever. It's impossible to recover, even with the most advanced forensic tools.
This is precisely why degaussing is classified as a "Purge" level sanitization method under strict guidelines like the NIST SP 800-88 publication. It doesn't just hide the data—it destroys its fundamental structure, resetting the media to a magnetically blank state.
Two Ways to Generate Magnetic Force
Degaussing machines create this powerful magnetic field using one of two core technologies. While the end result is the same—total data annihilation—the way they get there is a little different. Knowing the types helps you understand what tool is right for the job.
There are two main kinds of degaussers you'll run into:
- Coil (Electromagnetic) Degaussers: These are the workhorses of the commercial ITAD world. They use powerful electrical coils to generate a short but extremely intense electromagnetic pulse. Media passes through this field for a quick, complete sanitization cycle, making them perfect for processing huge volumes of drives.
- Permanent Magnet Degaussers: Just like the name implies, these machines use incredibly strong rare-earth magnets to create a constant magnetic field. They don't need electricity to generate the field (though they may need power for a conveyor belt), but the process can be a bit slower. They're a solid choice for smaller jobs or environments where reliable power is a concern.
Understanding Magnetic Field Strength
A degausser's power is measured in units called Oersteds (Oe) or Gauss. The media's coercivity is also measured in Oersteds. Here's the critical part: for a degauss to be successful, its field strength rating must be significantly higher than the media's coercivity—typically two to three times stronger.
For instance, a modern enterprise hard drive might have a coercivity of 5,000 Oe. To guarantee that drive is sanitized, you'd need a degausser that can generate a field of at least 10,000 Gauss.
Using an underpowered degausser is a massive security risk, as it could leave behind data fragments that are still recoverable. This is why it’s so important to work with a professional ITAD provider who uses certified, calibrated, and regularly tested equipment. The goal isn't just to wipe the media, but to permanently neutralize its ability to hold that old data.
Choosing the Right Degausser for Your Media
Not all data storage devices are created equal, and this is a critical distinction for any IT manager in charge of secure data destruction. While degaussing is a powerful, NIST-approved method for sanitizing magnetic media, trying to use it on the wrong device is like trying to erase a whiteboard with a kitchen magnet—it just won’t work.
Understanding which media types are compatible is the key to avoiding costly mistakes and ensuring your data sanitization process is actually secure. A degausser's power lies entirely in its ability to manipulate magnetic fields. This makes it the perfect tool for traditional spinning hard disk drives (HDDs) and magnetic backup tapes like LTO and DLT, which store data by arranging magnetic particles. A degausser is specifically designed to scramble that arrangement beyond recovery.
The Critical SSD and Flash Media Exception
This is where many organizations make a critical error. Degaussing is completely useless for modern Solid-State Drives (SSDs), USB flash drives, and other NAND flash-based media. These devices don’t store data magnetically; they rely on electronic charges stored in tiny flash memory cells.
Since there's no magnetic field to disrupt, even the most powerful degausser will have zero effect on the data stored on an SSD. This is a crucial point for any IT Asset Disposition (ITAD) strategy, especially as SSDs become more common in data centers and enterprise setups. Relying solely on degaussing creates a massive security gap. For more on managing modern assets, check out our guide on navigating data center equipment recycling.
For these non-magnetic media types, physical destruction through shredding is the only surefire method of data sanitization. It's the same story for optical media like CDs, DVDs, and Blu-ray discs, which store data in a physical layer read by a laser, making them immune to magnetic fields as well.
This simple decision tree shows how to pick the right approach based on your media.
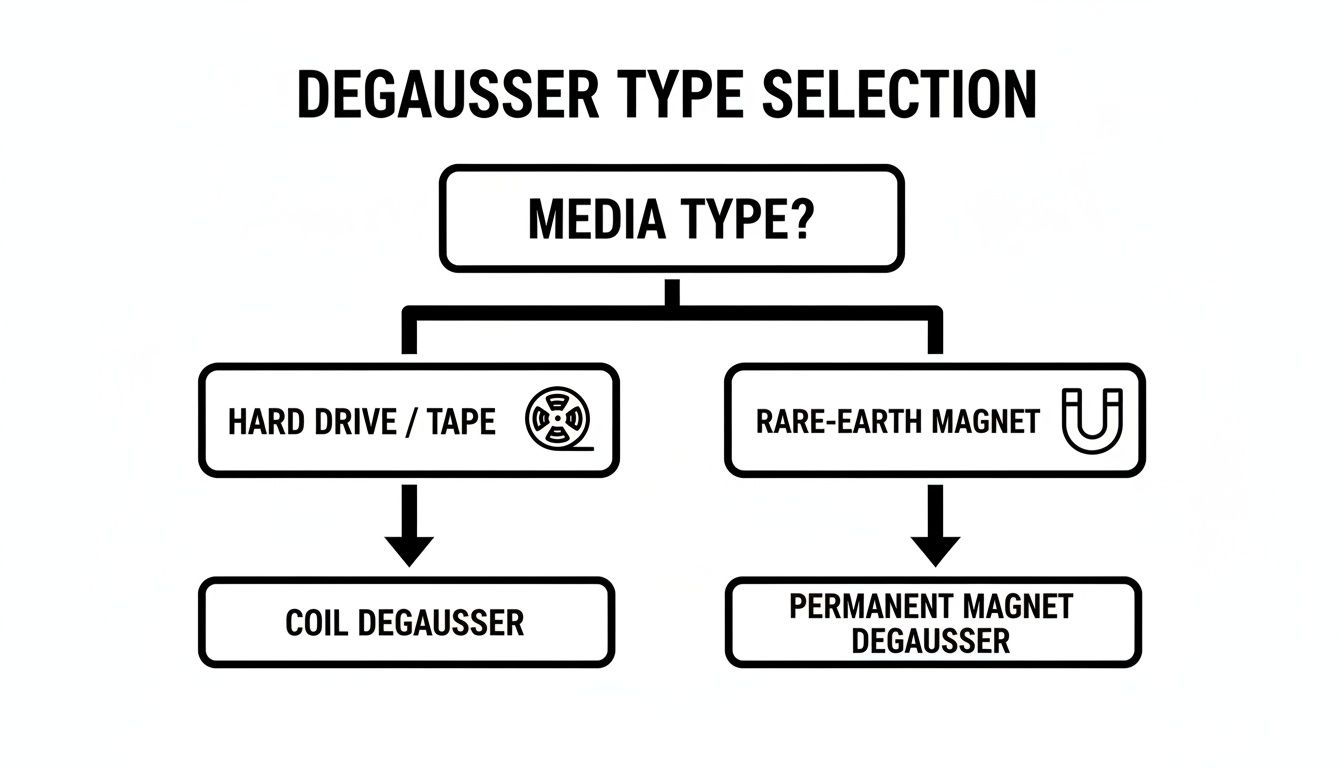
As you can see, the first question is always about the media type. Getting that right ensures you apply the correct technology from the start.
A Lesson from Naval History
The importance of matching technology to the target isn't a new concept. During World War II, the Navy had to meticulously calibrate degaussing systems on their ships to protect them from magnetic sea mines. Officers would board vessels, run them through test ranges, and fine-tune the electrical currents and cable turns to get the magnetic signature just right.
Just as the Navy had to adapt its methods for different ships and magnetic conditions, modern IT managers must adapt their data destruction methods for different storage media.
A common and dangerous assumption is that one data destruction method fits all devices. The truth is that using a degausser on an SSD is not just ineffective; it creates a false sense of security that can lead directly to a data breach.
To avoid this risk, you need a clear, documented process for identifying and segregating media types before any destruction begins.
This simple comparison can help guide your team's decisions on how to handle different types of media.
Media Compatibility for Data Destruction Methods
| Media Type | Degaussing | Shredding/Physical Destruction | Cryptographic Erasure/Wiping |
|---|---|---|---|
| HDDs (Hard Disk Drives) | Highly Effective | Highly Effective | Effective |
| Magnetic Tapes (LTO, DLT) | Highly Effective | Highly Effective | Not Applicable |
| SSDs (Solid-State Drives) | Ineffective | Highly Effective | Effective |
| USB Flash Drives | Ineffective | Highly Effective | Not Recommended |
| Optical Media (CD/DVD) | Ineffective | Highly Effective | Not Applicable |
This table clearly illustrates the specific roles each destruction method plays. By building an ITAD workflow that correctly identifies each asset and routes it to the right station—degausser, shredder, or software—your organization can maintain a secure and compliant chain of custody for all retired media.
Degaussing vs. Shredding vs. Wiping: A Practical Comparison

Picking the right data destruction method is a balancing act. You have to weigh your security needs, budget, and whether you want to get any value back from the old hardware. The three main pillars here are degaussing, shredding, and wiping, and each comes with its own set of pros and cons.
Getting this choice right is fundamental to any solid IT asset disposition (ITAD) strategy. It’s all about matching the method to your organization's specific goals.
Software Wiping: For Value Recovery
Software-based wiping is exactly what it sounds like: a program overwrites every inch of a drive with random ones and zeros, essentially burying the original data. Its biggest selling point is that the hard drive is still perfectly usable afterward. This means you can refurbish it, resell it, or put it back into service somewhere else.
This makes wiping the go-to choice when you want to maximize the return on your retired IT assets.
But it’s not perfect. Wiping is slow, sometimes taking hours for a single drive, which just isn't feasible when you're dealing with a large batch of equipment. Even more critically, the process can fail on drives that have bad sectors or physical damage, which could leave sensitive data recoverable. For anyone trading in personal electronics, knowing how to wipe your data is an absolute must-do first step.
Degaussing: For Absolute Magnetic Erasure
If you need speed and certainty for magnetic media, degaussing is your answer. In just a few seconds, a powerful magnetic field completely scrambles the underlying magnetic structure where data lives. It's permanent and completely unrecoverable.
This method is incredibly secure and works even on hard drives that are broken or too damaged to be wiped.
The big trade-off? A degaussed hard drive is nothing more than a paperweight. By destroying the low-level formatting and servo tracks that tell the drive how to operate, it becomes completely useless. This makes degaussing a fantastic, cost-effective solution when pure data security is the only goal, but it kills any chance of resale.
Physical Shredding: The Ultimate Proof
Physical shredding is the most visually satisfying and conclusive way to destroy data. It literally turns any storage device—including SSDs, which are immune to degaussing—into a pile of tiny, shredded fragments of metal and plastic. There’s no question about whether the data is gone. It offers the highest level of assurance.
Shredding provides an indisputable, physical end to the data lifecycle. For organizations requiring the highest level of security assurance or dealing with non-magnetic media, it is the industry-standard final step.
Just like degaussing, shredding completely destroys any potential for resale value. It’s the required method for devices holding top-secret government data, sensitive corporate R&D, and for all solid-state drives. For companies needing certified data destruction, Beyond Surplus offers comprehensive secure hard drive destruction services that meet the toughest compliance standards.
So, how do you choose? It all comes down to your priorities.
- Is asset value recovery the main goal? Software wiping is your best bet.
- Is absolute, rapid data destruction on magnetic media the priority? Degaussing is the clear winner.
- Do you need indisputable proof of destruction for SSDs or highly sensitive data? Shredding is the only answer.
Working With an ITAD Partner for Secure Degaussing Services
Knowing what a degausser does is one thing. Actually putting one to use correctly—and legally—is a whole different ballgame. For most companies, buying, maintaining, and operating a commercial degausser just isn't practical or cost-effective.
This is exactly where a certified IT Asset Disposition (ITAD) partner like Beyond Surplus comes in. The advantages are immediate and significant.
Outsourcing secure degaussing takes the huge capital expense of NSA-evaluated equipment right off the table. We’re talking tens of thousands of dollars saved from the start. It also gets rid of the ongoing headaches of maintenance, calibration, and training staff to run these powerful machines. More importantly, it transfers the operational risk from your team to ours.
Ensuring Compliance and Chain of Custody
A professional ITAD partner doesn’t just bring the machine; we bring a fully managed, auditable process. Every single step is meticulously documented to keep you compliant with standards like NIST SP 800-88 and privacy laws like HIPAA and GDPR. This is the bedrock of establishing a secure and unbroken chain of custody for your retired assets.
Once the data is gone for good, we issue a formal Certificate of Data Destruction. Think of this as your legal proof that the data was sanitized according to certified procedures. For any business in a regulated industry, this certificate is non-negotiable for passing audits and protecting you from liability.
Partnering with a certified ITAD provider transforms data destruction from a logistical burden into a streamlined, risk-managed service. It ensures that every asset is handled securely, compliantly, and with a clear, auditable trail from start to finish.
A Comprehensive and Managed Solution
An expert partner like Beyond Surplus handles the entire end-of-life asset workflow. This integrated approach covers every stage, giving you a single, reliable point of contact for everything. You can learn more about the complete lifecycle by exploring our detailed guide on what is IT asset disposition.
Our fully managed services include:
- Secure Logistics: We manage the secure packing and transportation of your assets from your facility to ours, using our own fleet and vetted partners.
- On-Site and Off-Site Services: We offer the flexibility of performing degaussing and shredding right at your location for total transparency, or at our secure, certified facility.
- Auditable Reporting: You get detailed inventory reports and serialized certificates, giving you a complete paper trail for your compliance needs.
- Responsible Recycling: After data destruction, all assets are processed through environmentally responsible recycling channels, helping you meet your corporate sustainability goals.
By entrusting your degaussing needs to a professional service, you get access to enterprise-grade tech and expertise without the overhead. This frees up your IT team to focus on what they do best—driving your business forward—while knowing your end-of-life data security is in expert hands.
Common Questions About Degaussing Technology
As more organizations bring degaussing into their data destruction workflows, a few practical questions always seem to pop up. Getting these details straight is the key to making smart, secure decisions about your IT asset disposition (ITAD) strategy. Here are the clear-cut answers to the questions we hear the most.
Does Degaussing Work on SSDs?
The short answer is a hard no. Degaussing is a magnetic process, built to scramble the tiny magnetic particles on traditional hard disk drives (HDDs) and tapes. Solid-State Drives (SSDs), on the other hand, don't store data magnetically at all. They use NAND flash memory, which works by trapping electrical charges in memory cells.
Since there’s no magnetic field to mess with, a degausser has zero effect on the data stored inside an SSD. Trying to degauss an SSD isn't just a waste of time; it creates a dangerous false sense of security that could easily lead to a data breach. For SSDs, the only NIST-approved sanitization method is physical destruction, which almost always means shredding.
Can You Reuse a Degaussed Hard Drive?
This is another common myth we need to bust. A degaussed hard drive is toast—it’s permanently inoperable and can never be used again. The intense magnetic pulse doesn't just wipe your data; it also destroys the drive's low-level formatting, including the firmware and servo tracks.
Think of those control tracks as the drive's internal GPS. They tell the read/write heads where to go on the platters. Without them, the drive is completely lost and can't function. It's now just a brick of metal and plastic. And that's exactly the point. Degaussing is a terminal process designed for total destruction, not refurbishment. If you're figuring out how to handle retired drives, our guide on what to do with old hard drives has some great pointers.
Is Degaussing More Secure Than Shredding?
That really depends on what you're destroying and your specific security needs. It's not a simple "one is better than the other" situation.
- For magnetic media (HDDs, Tapes): Degaussing is an incredibly secure method of data sanitization, making the data completely unrecoverable.
- For non-magnetic media (SSDs): Shredding is the only secure method.
Many organizations, especially those in highly regulated fields, take a belt-and-suspenders approach for maximum security. They degauss their magnetic hard drives first and then send them through the shredder afterward. This gives them an extra layer of assurance and creates an undeniable physical end to the asset's life.
Degaussing provides absolute data erasure for magnetic media, while shredding provides absolute physical destruction for all media types. The most secure protocol often involves both.
What Compliance Standards Does Degaussing Meet?
Certified degaussing is a globally recognized method for meeting the toughest data security and privacy regulations out there. The process aligns with the highest standards for media sanitization, including:
- NIST SP 800-88: The National Institute of Standards and Technology guidelines classify degaussing as a "Purge" level sanitization method, which is appropriate for destroying confidential data.
- DoD Requirements: It meets the Department of Defense standards for sanitizing magnetic media.
- HIPAA, GDPR, & FTC Disposal Rule: Degaussing helps organizations in healthcare, finance, and other regulated industries comply with data privacy laws by ensuring PII and sensitive information is permanently obliterated.
Working with a certified ITAD vendor is the best way to ensure the equipment and the entire process meet these critical benchmarks.
For certified degaussing, secure shredding, and comprehensive IT asset disposal services that meet the highest compliance standards, contact Beyond Surplus. We provide the expertise and documentation you need to manage your end-of-life IT assets with confidence. Learn more at https://atechdist.com.