Atlanta IT teams usually don’t decide to look for IT and telecom equipment disposal services because recycling suddenly became interesting. They look because a storage room is full, a lease return is due, a switch upgrade just finished, or an auditor asked what happened to retired drives. At that point, the problem isn’t old hardware. It’s unmanaged risk.
A pile of retired laptops, servers, phones, access points, and rack gear creates three problems at once. Sensitive data may still sit on drives and flash media. The business still owns the compliance obligation. And every week the assets sit untouched, resale value tends to get worse while internal handling gets messier.
That’s why disposal has to be treated as an operational function, not a cleanup task. If you’re working through Windows and server refresh cycles, IT support for Server 2012 R2 EOL is a useful reference for understanding how aging infrastructure decisions quickly turn into retirement and disposition decisions as well.
Introduction The End of Life Challenge for IT Assets
In Atlanta, this shows up in familiar ways. A data closet still holds decommissioned firewalls. A hospital IT team has carts of replaced workstations waiting for pickup. A multi-site company finished a telecom migration but never built a formal chain of custody for the equipment coming back from branch offices. The hardware may be out of production, but the liability isn’t.
The scale of the problem is much bigger than any one office. In 2022, the world generated 62 million tonnes of e-waste, and only 22.3% was formally collected and recycled, leaving US$62 billion in recoverable resources squandered, according to the UN Global E-waste Monitor 2024. For businesses, that’s not just an environmental headline. It’s a reminder that informal disposal channels are common, value is often lost, and accountability breaks down fast when assets leave the building without a documented process.
What disposal really means for an IT manager
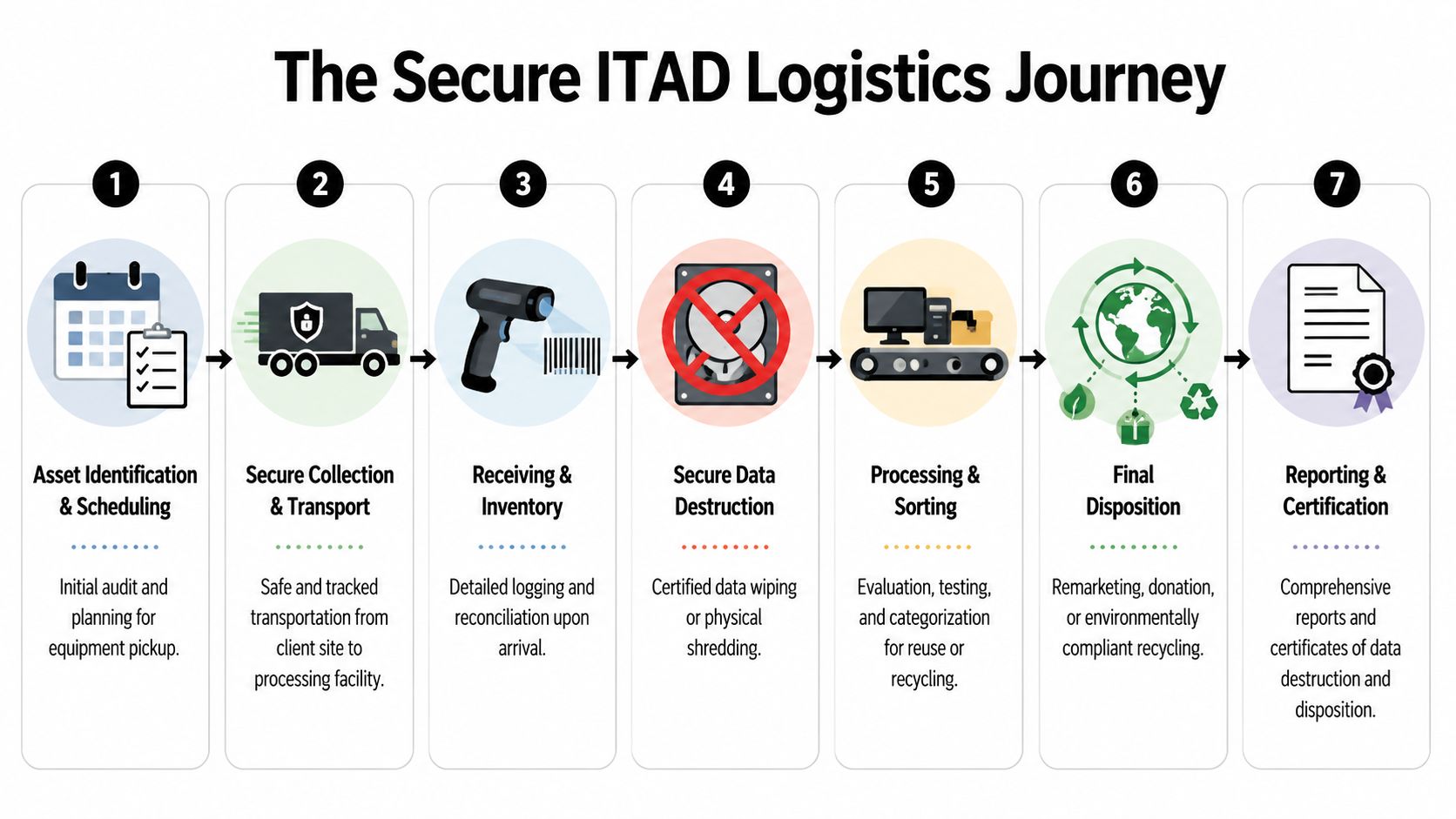
Professional IT and telecom equipment disposal services sit at the intersection of security, operations, and finance. The work includes identifying data-bearing devices, controlling pickup, documenting custody, deciding what can be reused, and proving what was destroyed or recycled.
A basic junk hauler can remove boxes. That doesn’t solve your exposure.
Practical rule: If a vendor can’t tell you how they track serialized assets, who handles data-bearing devices, and what documentation you’ll receive at the end, they’re not providing ITAD. They’re providing removal.
A structured end-of-life program also helps you plan, not just react. Teams that standardize retirement procedures usually handle refreshes faster because they know which assets can be redeployed, which need destruction, and which belong in a resale stream. For Georgia organizations, end-of-life IT asset management in Georgia is the kind of service model that reflects that broader business process.
Defining IT and Telecom Equipment Disposal Services
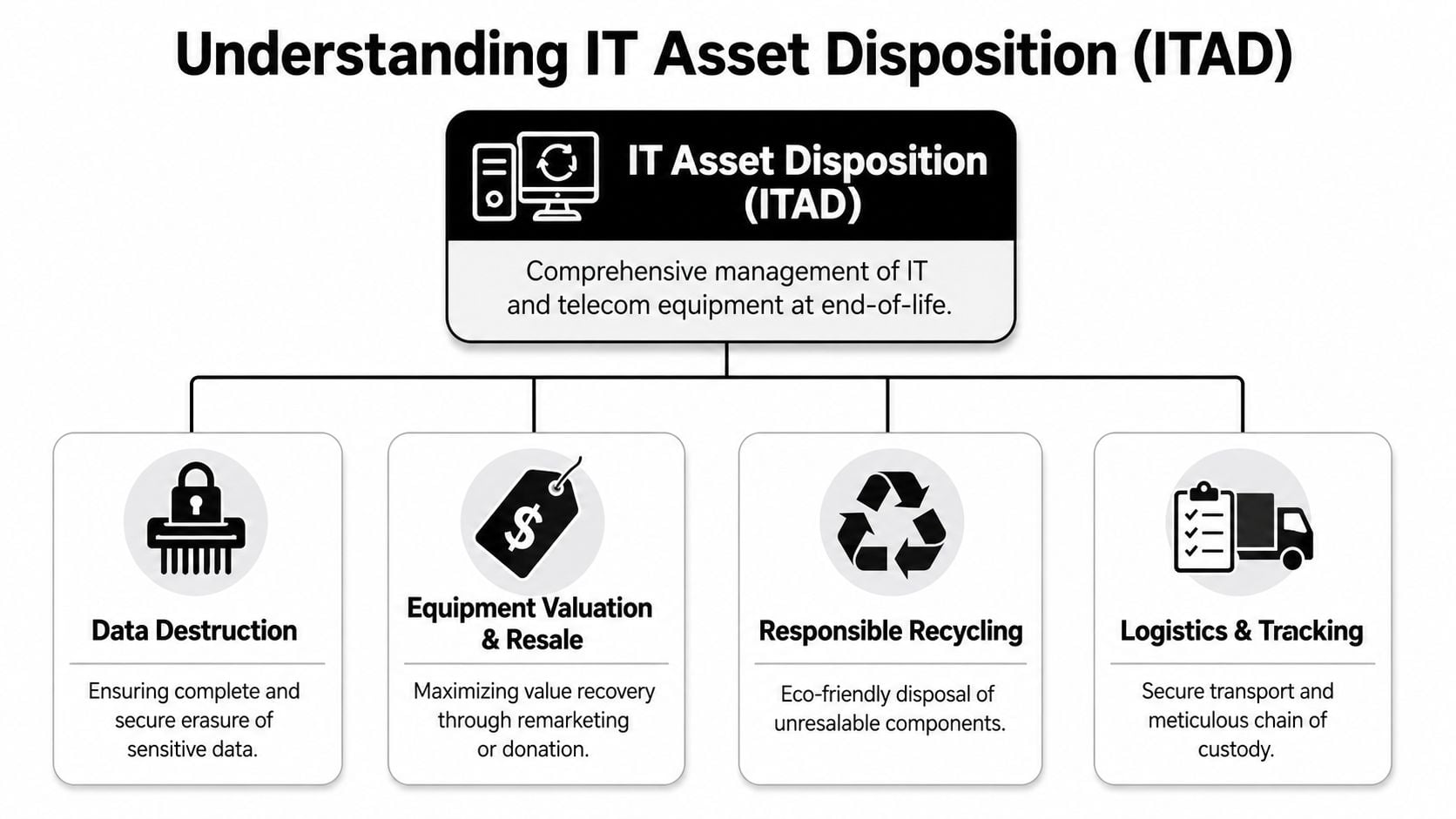
Most businesses use the word “disposal” too narrowly. In practice, IT Asset Disposition, or ITAD, is a managed workflow for retired technology. It covers devices with obvious storage, like servers and laptops, and devices people forget about, like VoIP phones, PBX hardware, printers, copiers, firewalls, routers, and wireless controllers.
That difference matters because ITAD is designed for business outcomes. A drop-off recycler focuses on material handling. An ITAD provider focuses on security, compliance, logistics, and value recovery.
The four parts that make ITAD work
Data destruction comes first because everything else depends on it. If the device stores credentials, customer records, call logs, network configs, or employee data, the sanitization method has to match the risk.
Equipment valuation and resale is where a lot of companies leave money on the table. Retired enterprise hardware may still have secondary market value if it’s tested, sorted correctly, and removed before it becomes too old to remarket.
Responsible recycling handles the gear that can’t be reused. That means disassembly, commodity recovery, and downstream processing through compliant channels rather than undocumented scrapping.
Logistics and tracking ties the whole process together. Without pickup controls, inventory reconciliation, and a documented chain of custody, even technically sound recycling can create an audit problem.
What ITAD is not
It isn’t office cleanout. It isn’t municipal e-waste day. It isn’t sending pallets to a warehouse and hoping the vendor “takes care of it.”
A real business process usually includes:
- Pre-pickup scoping: Reviewing asset types, site access, and handling requirements.
- On-site segregation: Separating data-bearing devices from non-data-bearing hardware.
- Inventory capture: Recording model, serial, and condition where needed.
- Disposition decisions: Reuse, resale, parts harvesting, recycling, or destruction.
- Final reporting: Certificates and asset-level documentation when required.
For organizations retiring phones, PBX systems, network hardware, and related gear, telecom equipment disposal services should include those controls, not just removal and recycling.
Good ITAD reduces uncertainty. That’s why mature IT teams treat it like a governed process with security and finance stakeholders involved, not a facilities afterthought.
The Critical Importance of Secure Data Destruction
A surprising number of businesses still think data destruction means deleting files, reformatting a drive, or trusting that a device “probably doesn’t store much.” That assumption is where breaches start. Telecom and IT hardware often holds far more than users expect, including cached credentials, call detail records, saved configurations, voicemail data, local logs, and exported reports.
NIST SP 800-88 provides the framework that matters most in practice. It defines Clear, Purge, and Destroy as the core sanitization levels. Physical destruction through shredding to specific particle sizes is the method that guarantees 0% data recovery, which is why it matters for strict compliance under rules such as HIPAA and the FTC Disposal Rule, as outlined in this overview of NIST SP 800-88 data destruction methods.

Clear when the reuse case is straightforward
Clear usually means overwriting the storage media. It’s appropriate when the risk is lower and the device is staying within a controlled reuse stream. In business terms, Clear works best when you know exactly what the device is, where it’s going next, and what level of assurance your policy allows.
The mistake is using Clear as a universal answer. It isn’t.
A firewall removed from a regulated environment may need a stronger method than a lab workstation being redeployed internally. The decision should come from data classification and compliance requirements, not convenience.
Purge when you need stronger assurance
Purge goes beyond standard overwriting. It includes methods such as degaussing or advanced overwriting intended to make recovery infeasible. This is often the middle ground for organizations that want to preserve some asset value while applying a more rigorous sanitization standard.
Purge is useful for equipment that may still be remarketed, especially when the hardware itself retains value but the stored data can’t be left to a basic wipe process. For many enterprise storage and network assets, that’s the practical sweet spot.
If a vendor only offers one destruction method for every asset class, they’re simplifying their operation at your expense.
Destroy when the risk is too high to tolerate
Destroy means physical destruction. Shredding is the clearest example. Once you choose Destroy, you’re prioritizing certainty over reuse, which is often the right call for failed drives, sensitive storage arrays, and gear from highly regulated departments.
That choice comes up more often than people think. Some devices are damaged, locked, encrypted in ways that complicate verification, or not worth the risk of any non-destructive process.
A useful cross-check is whether the provider can align destruction choices with your wider security standards. Teams that are already tightening connected device policies often benefit from broader security guidance like Sheridan Technologies' IoT security insights, because retired edge devices and telecom endpoints are part of that same attack surface lifecycle.
For organizations that need documented wiping, degaussing, or shredding workflows, enterprise data destruction in Georgia is the kind of service scope you should expect to evaluate.
Navigating Compliance and Regulatory Requirements
Compliance failures in asset disposal rarely come from dramatic misconduct. They usually come from weak process. A team retired equipment, got a pickup receipt, and assumed that was enough. Later, an internal audit asks for proof of destruction, proof of recycling, proof of downstream handling, and proof that liability didn’t remain with the original owner.
That’s where many programs fall short. A Certificate of Destruction is important, but it doesn’t answer every risk question.
Why documentation alone isn’t enough
True liability transfer goes beyond a standard certificate. Decision-makers need to vet a vendor’s insurance coverage, including environmental pollution insurance, audit history, and contractual indemnification clauses so the organization is protected if the ITAD partner later fails an audit or suffers a data breach, as discussed in this review of ITAD liability transfer considerations.
A certificate tells you something happened. It doesn’t automatically prove that the provider was properly insured, that downstream vendors were controlled, or that your contract allocated risk in a useful way.
What a careful buyer should ask for
When compliance is part of the disposal project, these questions matter:
- Insurance details: Ask what coverages are in force and request proof, not a verbal assurance.
- Audit posture: Ask whether the provider can explain recent compliance audits and corrective actions.
- Contract language: Review indemnification terms before scheduling pickup.
- Reporting depth: Confirm whether reports are aggregate only or asset-specific.
- Downstream transparency: Ask how non-resalable material is processed after initial handling.
Compliance is a vendor management issue as much as a disposal issue.
The same logic shows up in broader governance work. If you need a non-ITAD perspective on building control systems around regulated processes, Logical Commander on regulatory risk management is a useful companion read.
Teams that need sanitization standards mapped to documentation should also review NIST SP 800-88 guidance as part of vendor qualification. The key is consistency. Your internal policy, the vendor’s methods, and the final records all need to line up.
Mastering Logistics and Chain of Custody Management
Most disposal projects don’t fail at the shredder. They fail earlier, during movement. Hardware leaves a branch office without a proper manifest. Pallets sit overnight in an unsecured loading area. Equipment from multiple departments gets mixed together before inventory reconciliation. Once chain of custody gets blurry, every later document becomes less useful.
That’s why logistics deserves the same scrutiny as data destruction.
The handoff points that need control
For organizations with distributed infrastructure, reverse logistics can represent 15–30% of total disposition costs, yet it’s often poorly quantified. Effective ITAD partners address that with transparent planning and GPS-tracked transport for complex multi-site projects, as noted in this overview of enterprise reverse logistics for ITAD.
Those costs aren’t just freight. They include labor for de-installation, packing materials, liftgate requirements, site coordination, storage delays, and failed pickups when inventories aren’t ready.
A practical chain of custody model
A strong logistics process usually follows this order:
- Site scoping so the provider knows what’s coming, where it sits, and how it must be handled.
- Asset identification to separate reusable hardware, storage media, and regulated equipment.
- Secure pickup with controlled loading and transport records.
- Receiving reconciliation at the processing facility.
- Disposition reporting that matches what left your site.
If you’re planning a larger retirement event, especially involving racks, storage, and network equipment, data center decommissioning process guidance should be part of the planning conversation.
The best time to fix logistics is before pickup. After the truck leaves, undocumented assumptions turn into audit gaps.
What works and what doesn’t
What works is assigning an internal owner, freezing the asset list before pickup where possible, and requiring receiving reconciliation from the provider. What doesn’t work is mixing ad hoc office cleanout practices with enterprise IT disposal. They look similar from across the room. Operationally, they’re not.
Maximizing Value Recovery and Sustainability
A disciplined ITAD program does more than reduce exposure. It also helps recover value from hardware that still has useful life. That can mean resale of complete units, harvesting components, or routing certain devices into refurbishment rather than destruction.
This matters financially, but it also matters environmentally. Manufacturing a single computer and monitor requires at least 240 kg of fossil fuels, 22 kg of chemicals, and 1.5 tonnes of water, which is why refurbishment and component harvesting are central to closing the loop on IT assets, according to this analysis of global e-waste and resource intensity.

Recover value before age erodes it
The biggest operational mistake here is waiting too long. Equipment that could have entered a resale stream gets stacked in storage until market demand drops or the condition deteriorates. By then, the business pays handling costs without getting meaningful recovery.
A stronger model is to evaluate assets immediately after refresh or decommissioning. Working hardware can be tested and sorted quickly. Non-viable units can be stripped for parts or recycled through compliant downstream channels.
Sustainability works better when finance is involved
ESG goals often stay abstract until finance sees the connection between retained value and avoided waste. Once that happens, retirement timing improves. So does internal cooperation between IT, procurement, and facilities.
One provider in this space is Beyond Surplus, which offers IT equipment buy-back services alongside data destruction and recycling. That kind of combined model is useful because it lets organizations apply one intake process while separating devices into resale, parts recovery, and final recycling streams.
Reuse should be the first question for eligible hardware. Recycling is still necessary, but it’s the lower-value path when a device can be securely sanitized and remarketed.
Your Vendor Evaluation and Disposal Project Checklist
A good disposal project starts before the vendor arrives. The buyer has to define what’s being retired, what carries data, which sites are involved, and what records the business will need later. That preparation makes vendor comparison much easier because you’re asking each provider to solve the same problem.
Vendor evaluation questions that matter
Use these criteria when screening IT and telecom equipment disposal services:
- Security methods: Can the provider explain when they use wiping, degaussing, or shredding?
- Chain of custody: Do they document pickup, transport, receiving, and final disposition?
- Insurance and contract controls: Will they provide proof of coverage and clear indemnification language?
- Reporting quality: Can they issue the documentation your auditors or compliance team will request?
- Logistics capability: Can they handle multi-site pickups, de-installation, and scheduling without vague handoffs?
- Value recovery process: Do they have a credible method for testing and routing remarketable hardware?
A vendor that answers these clearly is usually operating from a real process. A vendor that stays vague is usually asking you to trust what should be documented.
Internal project checklist for your team
Before scheduling pickup, work through this sequence:
- Build the asset list. Identify device types, quantities, and locations.
- Flag data-bearing equipment. Include obvious storage devices and less obvious telecom and network gear.
- Separate by disposition intent. Decide what may be reused, remarketed, recycled, or destroyed.
- Confirm stakeholder requirements. Security, compliance, facilities, and finance should agree on the rules.
- Prepare the site. Stage assets, manage access, and prevent mix-ups with equipment still in service.
- Define documentation needs. Know what certificates and reports your organization requires.
- Review the vendor packet. Contract terms, insurance, scope, and scheduling should be settled before pickup day.
- Reconcile after processing. Match what left your site with what the provider reports.
That checklist sounds simple, but it prevents most of the disposal problems I see. Businesses get into trouble when they rush the handoff, skip internal alignment, or treat the project like a one-time cleanout instead of a controlled end-of-life process.
If your Atlanta team needs a documented path for retiring servers, laptops, storage, or telecom hardware, contact Beyond Surplus for certified electronics recycling and secure IT asset disposal.