An HDD destruction certificate is the official document that proves your company’s hard drives were physically destroyed, making the data on them gone for good. You can think of it as a death certificate for your data. It’s far more than a simple receipt—it's a legal record that shifts the liability for that data from your shoulders to a certified IT Asset Disposition (ITAD) provider like Beyond Surplus. For business owners, IT managers, and procurement professionals, understanding this document is a critical part of a modern data security strategy.
Your Shield Against Data Breaches and Fines

When your business retires old computers, servers, or storage equipment, just hitting "delete" on the files is a huge risk. Lingering data on those discarded hard drives is a major security hole waiting to be exposed. A single lost drive containing sensitive customer information, financial records, or company secrets can spiral into a devastating data breach.
This is where an HDD destruction certificate becomes your best defense. It serves as your auditable proof that your organization did everything right to prevent a breach. In today's world, this document is a non-negotiable part of modern risk management for any commercial enterprise, protecting your business from massive regulatory fines, lawsuits, and lasting damage to your brand’s reputation.
The Role of Certified Destruction in Modern Business
The need for verifiable data destruction isn't just a good idea; it's a critical business requirement. Growing concerns over data security and tough compliance rules have caused the secure destruction market to boom. This global industry was valued at USD 1.5 billion in 2023 and is expected to hit USD 3.6 billion by 2032, growing at a rate of 10.2% each year. This incredible growth shows just how seriously businesses are taking data security threats.
A certificate formally transfers responsibility for the data from your company to your destruction partner. It’s the tangible proof you need to show you’ve met your legal obligations under various data protection laws.
A valid HDD destruction certificate is your organization's formal record that it has taken definitive, verifiable steps to safeguard sensitive information. Without this documentation, your company remains fully liable for any data breach traced back to improperly disposed of hardware.
Why This Document Is Indispensable
For any business that handles sensitive information—from employee files to customer financial data—a destruction certificate is absolutely essential. It gives you the paperwork you need to satisfy auditors and prove you're compliant. This is especially true for companies in heavily regulated fields like healthcare (HIPAA), finance (GLBA), and government contracting.
So, what are the key benefits of getting a proper certificate?
- Liability Transfer: It legally moves the responsibility for data security from your company to the certified ITAD vendor.
- Compliance Verification: It offers auditable proof that you’ve followed data protection rules like NIST SP 800-88, FACTA, and GDPR.
- Risk Mitigation: It's a powerful tool for preventing the financial and reputational disaster that comes with a data breach.
- Peace of Mind: It gives you, your team, and your stakeholders confidence that your retired equipment won’t become a future security problem.
Ultimately, it’s crucial to see an HDD destruction certificate as an investment in security, not just another cost. To see how this process works from start to finish, you can learn more about Beyond Surplus's certified Certificate of Destruction services.
Decoding Your HDD Destruction Certificate
A real HDD destruction certificate is more than just a slip of paper; it’s a detailed legal document. Think of it like a car title or a property deed—every single detail counts because it has to hold up under the pressure of a compliance audit or legal inquiry. When you know what to look for, your IT team can spot red flags and make sure the paperwork you get offers ironclad proof of data security.

Just getting a document that says "Certificate of Destruction" isn't good enough. You have to check that it contains specific, auditable details that tie your physical hard drives directly to the destruction event. A generic certificate offers flimsy protection and could be disputed, leaving your organization completely exposed.
Core Elements of a Compliant Certificate
A strong certificate tells the whole story of what was destroyed, how it happened, and who is responsible. When you’re looking over documents from any ITAD provider, make sure it includes these essential components.
- Unique Certificate ID: This is a distinct tracking number for the certificate itself. It makes it easy to find and reference in your own records or during an audit.
- Client Information: Your company’s full legal name and address should be clearly listed, identifying you as the owner of the assets.
- ITAD Vendor Details: The full name, address, and contact info of the certified destruction partner, establishing who performed the service.
- Service Date and Location: The exact date the destruction occurred and where it happened—whether on-site at your building or off-site at the vendor’s facility.
These basic details are just the starting point. The real proof lies in the serialized inventory list, which provides the granular evidence needed for true compliance.
The Power of Serialized Tracking
The single most critical feature of a defensible HDD destruction certificate is a list of the unique serial numbers from every single hard drive. If a certificate just lists items in "bulk"—like "50 Laptops" or "1 Pallet of Hard Drives"—that is a major red flag.
Why does this matter so much? Without individual serial numbers, you can’t prove a specific drive was destroyed. Imagine a data breach happens and an investigator traces it back to a drive you thought was disposed of. A bulk certificate won't help you. It doesn't create the undeniable link between the asset that left your control and its final, confirmed destruction.
A non-serialized or "bulk" destruction certificate gives you a false sense of security. True liability transfer and legal protection are only achieved when every single data-bearing device is individually identified, tracked, and documented by its unique serial number.
A compliant certificate must have a detailed inventory that includes:
- Unique Serial Number: The manufacturer's serial number for each hard drive, SSD, or other device holding data.
- Asset Tag (If Applicable): Your own company's internal asset tag, which helps you cross-reference the device with your IT asset management system.
- Device Type/Model: A description of the item, such as "Seagate 1TB HDD" or "Dell Latitude E7470 Laptop."
This level of detail creates an unbroken, auditable paper trail. To get a better sense of what this looks like, you can check out our destruction certificate template to see how these parts are put together for maximum clarity and compliance.
Verifying the Method and Accountability
Finally, the certificate must clearly state the methods used and who is taking responsibility. Look for a straightforward declaration of the destruction technique—like physical shredding to a specific particle size (e.g., 2mm) or degaussing—and check that it meets standards such as NIST 800-88.
The document also needs an authorized signature from a representative of the ITAD vendor and a statement of indemnification. This legal clause is key—it confirms that the vendor takes on all liability for the data on the listed assets from the moment they collect them. This formally transfers the risk away from your organization for good.
Meeting Compliance Mandates with Certified Destruction
Think of an HDD destruction certificate as your official record for navigating today's complex data protection laws. It's far more than just an internal document; it's the definitive, auditable proof that shows auditors and regulators you’ve done your due diligence to secure sensitive information. This single piece of paper directly answers the core requirements of many different compliance rules.
For any business, compliance isn't a choice. Failing to correctly dispose of old hard drives and other data-storing devices can lead to some pretty serious consequences. The certificate of destruction acts as your primary evidence that your company took the "reasonable measures" needed to protect private information, a phrase you'll see in countless legal frameworks.
The High Stakes of Non-Compliance
Ignoring certified data destruction exposes your organization to major legal, financial, and reputational risks. Data protection authorities are handing out increasingly harsh penalties for non-compliance, turning what might seem like a simple oversight into a massive corporate headache. All it takes is one data breach from a carelessly discarded hard drive to destroy customer trust and permanently damage your brand.
The pressure is coming from all sides. Global regulations and the ever-present threat of a data breach have made the hdd destruction certificate a cornerstone of any solid compliance strategy. For example, Europe’s GDPR has already resulted in over €2.7 billion in fines since it took effect. Here in the U.S., the FTC Disposal Rule demands 'reasonable measures' for data erasure, and a certificate provides concrete legal proof of those actions.
The stakes are even higher in sectors like healthcare and finance. With HIPAA violations averaging $1.5 million in fines last year, it's no surprise that 65% of healthcare providers now partner with certified ITAD firms for disposal. This reality changes certified data destruction from a simple business cost into a critical investment in your company’s future.
Connecting Certificates to Key Regulations
An HDD destruction certificate gives you direct evidence of compliance with a whole range of data privacy laws. It closes the loop between your internal asset disposal policy and your external legal duties, creating a clear paper trail that will hold up under scrutiny.
Here’s how certified destruction lines up with some of the biggest regulations:
- HIPAA (Health Insurance Portability and Accountability Act): For any healthcare provider or business associate, a destruction certificate is essential. It proves that Protected Health Information (PHI) on old hard drives was made "unreadable, indecipherable, and otherwise cannot be reconstructed," which is exactly what the HIPAA Security Rule requires.
- GLBA (Gramm-Leach-Bliley Act): Financial institutions have a duty to protect consumers' private financial data. A certificate shows you’ve complied with the Safeguards Rule, which requires companies to secure customer information at every stage, including disposal.
- FACTA (Fair and Accurate Credit Transactions Act): This act demands the proper disposal of any consumer report information. A certificate of destruction confirms that your business followed FACTA’s Disposal Rule by physically destroying the media that held this sensitive data.
- GDPR (General Data Protection Regulation): Under GDPR, individuals have a "right to erasure." A certificate is your definitive proof that personal data has been permanently destroyed, fulfilling this key requirement and protecting you from massive fines.
By providing a detailed, serialized account of destroyed assets, the certificate acts as a legal shield. It formally documents that your organization fulfilled its duty of care, transferring liability and proving due diligence in the event of an audit or investigation.
This documentation is also crucial for proving you’ve followed specific data sanitization standards. Our process, for example, aligns with the guidelines in NIST SP 800-88, making sure the destruction methods meet or exceed federal recommendations. You can explore our guide on NIST 800-88 standards to get a better handle on these requirements. Working with a certified vendor like Beyond Surplus ensures your disposal process isn't just secure, but fully compliant.
On-Site vs. Off-Site Destruction: A Commercial Guide
When it comes to the final, physical destruction of your hard drives, your business has two primary paths: on-site and off-site destruction. The right choice depends on your organization’s security policies, budget, and the volume of drives requiring disposal. Both are secure, compliant methods when performed by a certified ITAD partner.
On-site destruction is exactly what it sounds like. A mobile shredding truck comes directly to your business location. This option offers maximum transparency, as your team can witness every drive being fed into the shredder and rendered into unrecoverable fragments.
Off-site destruction involves having your assets securely transported to a dedicated, high-security destruction plant. While you won't see the shredding happen in person, a certified ITAD partner like Beyond Surplus follows a strict, documented chain of custody from the moment the drives leave your facility until they are destroyed. It’s often the more practical and cost-effective choice for large-scale enterprise projects.
The Case for On-Site Destruction
The primary reason businesses choose on-site destruction is for maximum security assurance. The chain of custody is absolute, as hard drives never leave your property intact, eliminating all transportation risks.
- Total Transparency: Your staff can witness the entire process, confirming that every drive is destroyed according to your company's security standards.
- Instant Confirmation: The job is completed on-site, and you receive your HDD destruction certificate immediately, closing the compliance loop.
- Ideal for High-Risk Data: For classified data, sensitive intellectual property, or assets under strict government regulations, on-site destruction is the gold standard.
This method provides unparalleled peace of mind for organizations where the perception of security is as critical as the reality. To see how this works, check out how Beyond Surplus provides secure on-site data destruction services.
On-Site vs. Off-Site HDD Destruction: A Comparison
Choosing between on-site and off-site destruction is a strategic business decision. Both methods are secure and compliant when executed correctly, but they cater to different operational priorities. This table breaks down the key differences to help you decide which approach fits your business best.
| Feature | On-Site Destruction | Off-Site Destruction |
|---|---|---|
| Security | Maximum. Drives are destroyed before leaving your premises. No transit risk. | High. Relies on a secure, audited chain of custody and a fortified facility. |
| Verification | Direct visual confirmation. You can witness the entire process firsthand. | Documented proof. Verified through a serialized Certificate of Destruction. |
| Cost | Generally higher due to dedicated equipment and personnel at your location. | More cost-effective, especially for large volumes, due to economies of scale. |
| Logistics | Requires scheduling and providing space for a large mobile shred truck. | Simpler logistics. The vendor handles secure pickup and transport. |
| Scalability | Good for moderate volumes, but can be slower for massive quantities. | Highly scalable. Ideal for data center decommissioning or large enterprise projects. |
| Best For | High-security needs, compliance-heavy industries, and absolute peace of mind. | Cost-conscious businesses, large-volume disposals, and routine IT asset refreshes. |
Ultimately, both on-site and off-site destruction are valid, defensible methods. Your choice depends on whether you prioritize witnessed security over cost-efficiency and scalability.
The Case for Off-Site Destruction
For many businesses, off-site destruction provides the perfect balance of security, efficiency, and cost-effectiveness without compromising compliance. The critical factor is partnering with a vendor who can demonstrate a robust, auditable chain of custody.
- Cost-Effectiveness: Off-site services are typically more affordable as the vendor processes assets from multiple clients in large batches, creating economies of scale that reduce your costs.
- Scalability and Efficiency: A dedicated facility is built to handle massive volumes of drives far more quickly than a mobile truck, making it ideal for large-scale projects like data center decommissioning.
- Verified Security: Certified destruction plants are secure facilities with 24/7 surveillance, restricted access, and audited procedures that often exceed what is possible with a mobile unit.
As long as it's backed by a strong chain of custody, off-site destruction gives you the same legal and compliance protection as on-site services. A serialized certificate of destruction from a NAID AAA certified facility is just as valid and defensible in an audit.
The decision is a business one. If your company requires absolute, witnessed certainty and the budget allows, on-site is an excellent choice. However, for a secure, efficient, and scalable solution for a large number of assets, off-site destruction with a trusted partner is a smart and practical commercial decision.
Why Chain of Custody Is Your Process's Backbone
A destruction certificate is only as strong as the security process behind it. Think of the chain of custody as the unbroken, documented trail that tracks your hard drives from the moment they leave your hands to their final, verified destruction. This process is the logistical and security backbone that gives your hdd destruction certificate its real authority.
Imagine it's like handling evidence in a legal case. If there's any gap in the documentation—any point where an asset is unaccounted for—the integrity of the entire process is thrown into question. One missing link can make your certificate of destruction worthless, leaving your organization exposed to massive risk and liability. A weak chain of custody means the final certificate is just a piece of paper.
The Critical Stages of a Secure Chain of Custody
A truly secure process is meticulous, transparent, and documented every step of the way. It’s not enough for a vendor to just say they have a secure process; they need to prove it with a record you can audit. This involves several non-negotiable stages.
- Secure Collection and Asset Tagging: The process kicks off at your location. Every single data-bearing device is inventoried by its unique serial number and your company’s asset tag. This initial scan is the foundation for everything that follows.
- Locked and Sealed Transport: Your assets are then placed into locked, tamper-evident containers before being loaded onto a GPS-tracked vehicle. This ensures nothing can be accessed or sneakily removed during transit.
- Controlled Facility Access: Once at the destruction facility, the sealed containers are opened inside a secure, monitored area. The assets are scanned again to confirm that every item that left your facility has arrived safely for destruction.
- Documented Destruction: The final destruction is recorded, creating a permanent link between each serial number and the exact date, time, and method of destruction.
This flowchart shows how the process works for both on-site and off-site destruction, highlighting how a proper chain of custody is maintained no matter which option you choose.
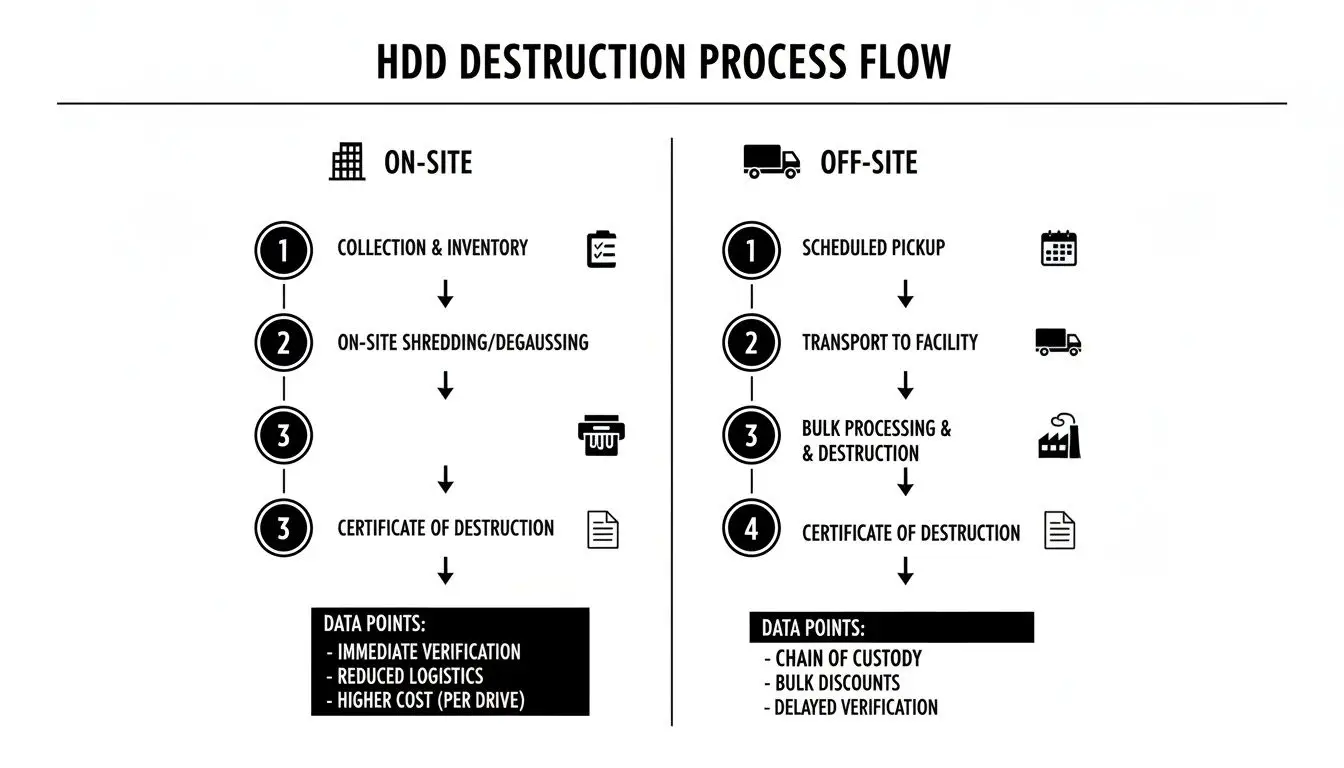
As you can see, whether destruction happens at your site or ours, a serialized and documented process is the key to creating an audit trail that will stand up to scrutiny.
Why an Auditable Trail Is Non-Negotiable
Federal and state laws are increasingly demanding proof of secure disposal, which makes a rock-solid chain of custody essential. This is especially true for data centers. Verizon's 2025 DBIR pointed out that 74% of breaches involved a human element, which absolutely includes improper hardware disposal. On top of that, a 2026 Deloitte poll found that 85% of IT managers said destruction certificates—validated by a strong chain of custody—were a key factor in choosing an ITAD vendor.
A documented chain of custody is what turns a simple receipt into a legally defensible HDD destruction certificate. Without it, you have no verifiable proof, and your organization holds all the risk.
Ultimately, the certificate you get is the final chapter of a story that starts the moment your assets are collected. When you partner with a certified ITAD vendor like Beyond Surplus that guarantees a transparent, serialized chain of custody, you ensure that certificate provides the airtight legal protection your business needs. You can learn more about how ownership is formally transferred in our guide on the essential title transfer process for your assets.
Your HDD Destruction Certificate Questions Answered
Even after you’ve got a handle on the process, some specific questions almost always pop up when you're putting a secure data destruction policy into practice. This is where we clear up the most common and pressing questions businesses have about HDD destruction certificates and the processes behind them. The answers here are direct, practical, and drive home the key points from this guide.
How Long Should My Business Keep an HDD Destruction Certificate?
It’s best to think of your HDD destruction certificate as permanent legal proof. While there isn't one single federal law that sets a retention period for every type of business, the best practice is to hold onto these certificates indefinitely.
At the absolute minimum, you should keep them for at least seven years. This timeline lines up with the statute of limitations for many legal and regulatory actions. If an audit, legal dispute, or data breach investigation ever comes up—even years down the road—this certificate is your go-to evidence that you did your due diligence and properly transferred liability.
In legal and compliance matters, the burden of proof is on your organization. Not being able to produce a certificate for a past disposal event is often seen as a failure to perform that due diligence.
Storing these documents digitally in a secure, backed-up, and easy-to-find location is a cornerstone of smart, long-term risk management. A solid digital archive means you can pull up proof of destruction whenever you need it, protecting your organization long after the assets themselves are gone. At Beyond Surplus, we provide digital copies of all certificates to our clients to make this critical step simple.
Is a Certificate of Recycling the Same as a Certificate of Destruction?
No, and this is a critical difference that can create major compliance gaps. Mixing these two documents up is a common and dangerous mistake that leaves your company’s sensitive data completely exposed.
A Certificate of Recycling is all about environmental liability. It confirms that your electronic waste was processed in an environmentally sound way, following regulations from agencies like the EPA, and that hazardous materials didn't just get dumped in a landfill.
An HDD Destruction Certificate, on the other hand, deals only with data security liability. It provides auditable proof that the data-storing devices were physically destroyed, making the information on them permanently unrecoverable.
Here’s an easy way to think about it:
- Certificate of Recycling: Proves you met your environmental duties.
- Certificate of Destruction: Proves you met your data security duties.
A full-service, certified ITAD partner like Beyond Surplus will give you both documents as part of a complete asset disposal project, but they serve two very different functions. You absolutely must get a specific, serialized Certificate of Data Destruction for every single device that ever held sensitive information. One protects you from environmental fines; the other protects you from a data breach.
What If My Vendor Provides a Non-Serialized Certificate?
A non-serialized or "bulk" certificate is a huge red flag. This kind of document, which might list items in generic terms like "100 Hard Drives" or "2 Pallets of IT Equipment," gives you incredibly weak legal protection and should be a deal-breaker for any business.
Without individual serial numbers tying each specific hard drive to the destruction event, you have no way to prove a particular asset was actually destroyed. If a drive you thought was disposed of later shows up in a data breach, a bulk certificate won't help you. You can't prove that the compromised drive was part of that batch, which means your organization is still on the hook for the breach and all its consequences.
A serialized inventory is the only thing that creates an unbreakable, auditable link between an asset leaving your control and its confirmed destruction. Without it, the certificate is merely a receipt for service, not a transfer of liability.
Always insist on a serialized certificate that lists every single data-bearing asset by its manufacturer serial number. A reputable, certified vendor will provide this as a standard, non-negotiable part of their service. If a potential partner can’t—or won’t—provide one, it's a clear sign their processes aren't rigorous enough for real compliance and risk management.
Can I Trust a Certificate from Any E-Waste Recycler?
Not all certificates hold the same weight or offer the same level of legal protection. The real value of an HDD destruction certificate is tied directly to the credibility, processes, and certifications of the vendor who issues it.
When you’re looking at a potential ITAD partner, you have to look past their marketing and verify their credentials. The most respected and demanding third-party certifications in the industry include:
- NAID AAA Certification: This is the gold standard specifically for data destruction. NAID (the National Association for Information Destruction) conducts unannounced audits to verify a vendor’s security, employee screening, and destruction methods meet the highest industry standards. A certificate from a NAID AAA certified vendor gives you the strongest possible proof that the process is secure, compliant, and defensible.
- R2v3 (Sustainable Electronics Reuse & Recycling) Certification: This certification focuses on environmental responsibility, safety, and data security throughout the entire electronics recycling lifecycle.
- e-Stewards Certification: Another top environmental and social responsibility standard that also includes strict requirements for data security and bans the export of hazardous e-waste.
A certificate from a vendor with these credentials—especially NAID AAA—is much more than a piece of paper. It's proof that their entire operation has been checked and approved by an independent body, making sure their promises of security and compliance are backed by audited practices.
Managing the end-of-life for your IT assets is a critical job that comes with significant risk. An HDD destruction certificate, backed by a secure chain of custody and issued by a certified vendor, is your most powerful tool for handling that risk. Contact Beyond Surplus for certified electronics recycling and secure IT asset disposal. Learn more about our nationwide services for businesses at https://atechdist.com.